|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> PHProxy Detection Vulnerability Assessment Details
|
PHProxy Detection |
||
|
Searches for the existence of PHProxy Detailed Explanation for this Vulnerability Assessment Summary : The remote web server contains an HTTP proxy written in PHP. Description : The remote host is running PHProxy, a PHP-based HTTP proxy intended to bypass firewall and other proxy restrictions. See also : http://whitefyre.com/poxy/ Solution : Make sure use of this program is in accordance with your corporate security policy. Network Security Threat Level: None Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2007 Tenable Network Security |
||
|
Cables, Connectors |

Apollo Vampire 600v2 / 600 V2 FPGA Accelerator Card for Commodore Amiga 600
$350.00
Mini External OLED AMIGA Gotek Floppy Drive Emulator For Amiga 500/500+/600/1200
$40.46
Pacific Cypress Xpander II 2 MB Ram Board AMIGA READ UNTESTED
$299.95
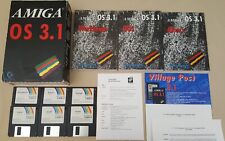
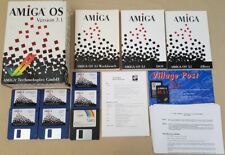
Amiga OS Operating System v3.1 Box Manuals & Install Disks for Amiga - Commodore
$289.98
Amiga OS Operating System v3.1 Box Manuals & Install Disks for Amiga - Escom
$289.98
Amiga OS Operating System v3.1 ROM & Install Disks for Commodore Amiga 500 2000
$49.98
Amiga OS Operating System v3.1 Install Disks for Commodore Amiga
$34.98
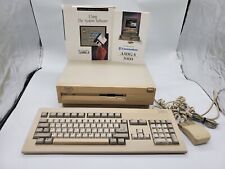
Commodore Amiga 3000 030 25Mhz + Keyboard + Mouse - Amiga OS 3.2 - WORKS 100%
$1599.99
AMIGA 500 COMPUTER COMMODORE Complete in Box Powers/untested Good Condition
$370.00
pi1541 Disk Emulator for Commodore -
$38.95
|
||
|
No Discussions have been posted on this vulnerability. |