|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> PHPNews sendtofriend.php SQL injection Vulnerability Assessment Details
|
PHPNews sendtofriend.php SQL injection |
||
|
Makes a request to the remote host by supplying the mid paramter in the url Detailed Explanation for this Vulnerability Assessment The remote host is using PHPNews, an open source news application. It utilizes database to store the content. A vulnerability exists in the remote version of this software which may permit a possible hacker to inject arbitrary SQL code and possibly execute arbitrary code, due to improper validation of user supplied input in the 'mid' parameter of script 'sendtofriend.php'. Solution : Upgrade to the version 1.2.4 of this software Network Security Threat Level: High Networks Security ID: 11748 Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security. |
||
|
Cables, Connectors |

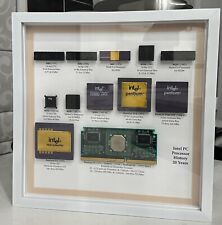
Vintage Intel Personal PC CPU Collection in White Shadowbox Display
$200.00
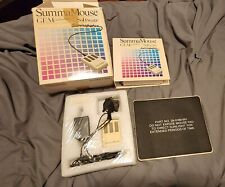
VINTAGE SummaGraphics SummaMouse
$240.00
Vintage Classic Apple Macintosh System Boot Install Disk Floppy/CD *Pick Version
$10.39
Z80 - NABU PC & Keyboard - Vintage New Old Stock (Retro 80's)
$139.99
Drakware ADB2USB - vintage Apple ADB to USB keyboard adapter
$29.95
Vintage Compaq 141649-004 2 Button PS/2 Gray Mouse M-S34 - FAST SHIPPING - NEW
$8.99
Vintage Black Microsoft intellimouse Optical USB Wheel Mouse 1.1/1.1a - EXC COND
$28.95
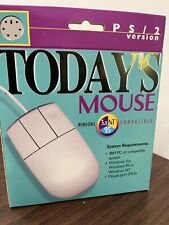
Vintage Computer Mouse - Todays Mouse - Windows 95 P S/2
$9.99
SEALED Vintage Western Digital Value Line Hard Drive 3.5-Inch Enhanced IDE 25 GB
$100.00
Vintage Compaq Presario Mouse, Model MUS9J, PS/2 - Tested & Working, Very Good
$12.99
|
||
|
No Discussions have been posted on this vulnerability. |