|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Windows >> Opera < 8.02 Multiple Vulnerabilities Vulnerability Assessment Details
|
Opera < 8.02 Multiple Vulnerabilities |
||
|
Checks for multiple vulnerabilities in Opera < 8.02 Detailed Explanation for this Vulnerability Assessment Summary : The remote host contains a web browser which is affected by multiple issues. Description : The remote host is using Opera, an alternative web browser. The version of Opera installed on the remote host contains several flaws. One involves imaging dragging and could result in cross-site scripting attacks and user file retrieval. A second may let attackers spoof the file extension in the file download dialog provided the 'Arial Unicode MS' font has been installed, which is the case with various Microsoft Office products. And a third is a design error in the processing of mouse clicks in new browser windows that may be exploited to trick a user into downloading and executing arbitrary programs on the affected host. See also : http://secunia.com/advisories/15756/ http://secunia.com/advisories/15870/ http://secunia.com/secunia_research/2005-19/advisory/ Solution : Upgrade to Opera 8.02 or later. Network Security Threat Level: Medium / CVSS Base Score : 6 (AV:R/AC:H/Au:NR/C:P/A:P/I:P/B:N) Networks Security ID: 14402, 14410, 15835 Vulnerability Assessment Copyright: This script is Copyright (C) 2005-2006 Tenable Network Security |
||
|
Cables, Connectors |

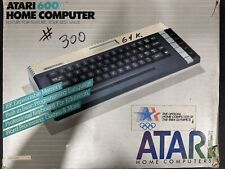
Atari 600 XL Vintage Home Computer - IN BOX W/ Manuals, Cables. Clean Console
$175.00
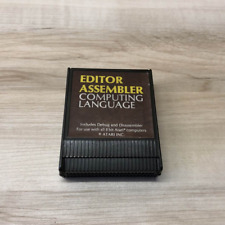
EDITOR ASSEMBLER : Computing Language Original ATARI 400/800 Computer Cartridge
$40.00
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
A8PicoCart Kit Atari XE XL unocart clone multicart cartridge game
$18.95
TEAM TAP Atari Jaguar Multi Player Adapter Used (no box) - Tested
$12.00
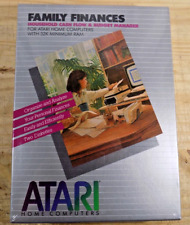
ATARI Home Computers FAMILY FINANCES Software **SEALED NEW** 1982
$25.00
Vintage Atari 800XL Computer With Original Box
$140.00
Rare Vintage Atari XF551 Floppy Disk Drive Station for 400, 800, 600, XE and XL
$300.00
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
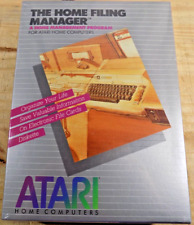
ATARI Home Computers HOME FILING MANAGER Software **SEALED NEW** 1982
$25.00
|
||
|
No Discussions have been posted on this vulnerability. |