|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gain root remotely >> OpenSSH Channel Code Off by 1 Vulnerability Assessment Details
|
OpenSSH Channel Code Off by 1 |
||
|
Checks for the remote OpenSSH version Detailed Explanation for this Vulnerability Assessment You are running a version of OpenSSH which is older than 3.1. Versions prior than 3.1 are vulnerable to an off by one error that permits local users to gain root access, and it may be possible for remote users to similarly compromise the daemon for remote access. In addition, a vulnerable SSH client may be compromised by connecting to a malicious SSH daemon that exploits this vulnerability in the client code, thus compromising the client system. Solution : Upgrade to OpenSSH 3.1 or apply the patch for prior versions. (See: http://www.openssh.org) Network Security Threat Level: High Networks Security ID: 4241 Vulnerability Assessment Copyright: This script is Copyright (c) 2002 Thomas Reinke |
||
|
Cables, Connectors |

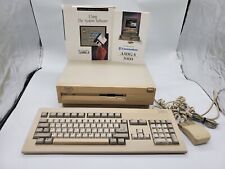
Commodore Amiga A1200 Computer Keyboard Untested *AS IS* Read Description
$5000.00
Mini External OLED AMIGA Gotek Floppy Drive Emulator For Amiga 500/500+/600/1200
$39.20
Commodore Amiga 3000 030 25Mhz + Keyboard + Mouse - Amiga OS 3.2 - WORKS 100%
$1599.99
Brand New Amiga 4000T Keyboard
$299.99
Amiga Aminet 10 February 96 1996 Commodore
$13.20
Amiga 500 Gotek Custom Mount USB Floppy Emulator - Complete Kit with Gotek
$65.00
Commodore Amiga 1060 Side Car Expansion "IBM PC EMULATOR" VERY RARE COLLECTIBLE
$1499.95
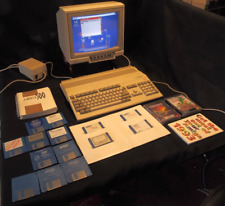
Commodore Amiga 500 with Original Box. Power Supply Games and More 1 MEG No.2
$462.36
AMIGA 500 COMPUTER COMMODORE Complete in Box Powers/untested Good Condition
$370.00
Amiga 5.25 External DUAL SLIM Floppy Disk Drive VERY RARE
$199.00
|
||
|
No Discussions have been posted on this vulnerability. |