|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gain root remotely >> OpenSSH AFS/Kerberos ticket/token passing Vulnerability Assessment Details
|
OpenSSH AFS/Kerberos ticket/token passing |
||
|
Checks for the remote SSH version Detailed Explanation for this Vulnerability Assessment You are running a version of OpenSSH older than OpenSSH 3.2.1 A buffer overflow exists in the daemon if AFS is enabled on your system, or if the options KerberosTgtPassing or AFSTokenPassing are enabled. Even in this scenario, the vulnerability may be avoided by enabling UsePrivilegeSeparation. Versions prior to 2.9.9 are vulnerable to a remote root exploit. Versions prior to 3.2.1 are vulnerable to a local root exploit. Solution : Upgrade to the latest version of OpenSSH Network Security Threat Level: High Networks Security ID: 4560 Vulnerability Assessment Copyright: This script is Copyright (C) 2002 Thomas Reinke |
||
|
Cables, Connectors |

Vintage Iomega Zip 250 250MB w/ USB Cable Untested
$45.00
Vintage Computer Mouse - Todays Mouse - Windows 95 P S/2
$9.99
Drakware ADB2USB - vintage Apple ADB to USB keyboard adapter
$29.95
Vintage Apple Lisa Brochure, very nice condition
$50.00
Vintage Classic Apple Macintosh System Boot Install Disk Floppy/CD *Pick Version
$10.39
Vintage Compaq 141649-004 2 Button PS/2 Gray Mouse M-S34 - FAST SHIPPING - NEW
$8.99
Z80 - NABU PC & Keyboard - Vintage New Old Stock (Retro 80's)
$139.99
Vintage Black Microsoft intellimouse Optical USB Wheel Mouse 1.1/1.1a - EXC COND
$28.95
RARE Vintage CVT Avant Stellar GT6OMNIKEY Mechanical Programmable Keyboard BLACK
$249.99
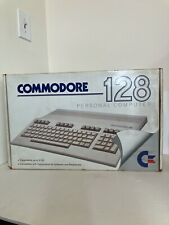
Vintage Commodore 128 Personal Computer w/Box 1987 Untested As Is Rare
$249.99
|
||
|
No Discussions have been posted on this vulnerability. |