|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Open WebMail Detection Vulnerability Assessment Details
|
Open WebMail Detection |
||
|
Searches for the existence of Open WebMail Detailed Explanation for this Vulnerability Assessment Summary : The remote web server contains a webmail application. Description : This script detects whether the target is running Open WebMail and extracts version numbers and locations of any instances found. Open WebMail is a webmail package written in Perl that provides access to mail accounts via POP3 or IMAP. See also : http://www.openwebmail.org/ Network Security Threat Level: None Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 George A. Theall |
||
|
Cables, Connectors |

Cisco SG95-16 16-Port Gigabit Switch SG95-16-KR
$47.00
8 Ports Unmanaged Industrial Ethernet Switch Network Gigabit Ethernet Switch
$76.50
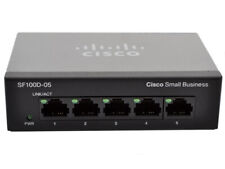
Cisco (SG100D-05-UK) 5-Ports External Ethernet Switch
$40.00
100Mbps Fiber Optic Media Converter 16 SC Optical Port 2 RJ45 10/100/1000Mbps
$462.99
HP 2530-48G 48 Port Gigabit Ethernet Network Switch J9775A
$30.95
New Linksys SE3005 5-port Gigabit Ethernet Switch
$18.99
Linksys SE3008 8 Ports Rack Mountable Gigabit Ethernet Switch
$21.99
HP ProCurve 2530-24G J9776A 24 Port Gigabit Ethernet Managed Network Switch
$34.99
Juniper Networks EX3300-48P 48-Port PoE+ 4x SFP+ Network Switch w/ Power Cord
$43.95
Netgear Prosafe Plus JGS524PE 24 Port Gigabit Switch 12 Port PoE JGS524PE-100NAS
$129.98
|
||
|
No Discussions have been posted on this vulnerability. |