|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Windows >> Novell Client nwspool.dll Buffer Overflow Vulnerability Vulnerability Assessment Details
|
Novell Client nwspool.dll Buffer Overflow Vulnerability |
||
|
Checks file version of nwspool.dll Detailed Explanation for this Vulnerability Assessment Summary : The remote Windows host contains a DLL that suffers from a buffer overflow flaw. Description : The file 'nwspool.dll' included with the Novell Client software reportedly contains a buffer overflow that can be triggered by long arguments to the Win32 'EnumPrinters()' and 'OpenPrinter()' functions. An anonymous remote attacker may be able to leverage this issue via RPC requests to the Spooler service to execute arbitrary code remotely on the affected host. See also : http://www.zerodayinitiative.com/advisories/ZDI-06-043.html http://www.securityfocus.com/archive/1/archive/1/453012/100/0/threaded http://support.novell.com/cgi-bin/search/searchtid.cgi?/2974765.htm Solution : Install the 491psp3_nwspool.exe patch file referenced in the vendor advisory above. Network Security Threat Level: High / CVSS Base Score : 7.0 (AV:R/AC:L/Au:NR/C:P/I:P/A:P/B:N) Networks Security ID: 21220 Vulnerability Assessment Copyright: This script is Copyright (C) 2006-2007 Tenable Network Security |
||
|
Cables, Connectors |

Macintosh Platinum Mouse - Apple 128K 512K 512Ke Mac Plus Lisa IIe M0100 - NEW
$44.99
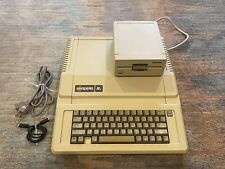
Apple IIe Computer - 128k Enhanced w/ 80col + 5.25 Drive Card + Serial Card
$349.00
Vintage Apple lle 128k Enhanced Computer A2S2064 Rebuilt W/ Disk Drive & more
$389.99
Apple Macintosh 128k 512k Plus Analog Board Capacitor Re-Cap Kit - US Shipping
$23.95
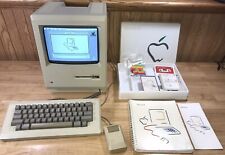
1984 APPLE MACINTOSH Model M0001 1st MAC 128K 40th Anniversary PICASSO KIT NICE
$4999.99
Apple Macintosh 128K M0001 Computer with 128K Label - Estate Sale SOLD AS IS
$2468.10
Apple Macintosh Mac 128K M0001 Computer 1984 w/Keyboard M0110 Mouse M0100 & Bag
$849.99
Vintage M0001 Macintosh 128 128K Computer 1984 Front Cover Nice
$79.00
Apple Macintosh 128K Parts Kit - P/N 073-0140-A
$273.60
Apple Macintosh 128K M0001 Computer with Mouse, no keyboard. Case included. 1984
$507.01
|
||
|
No Discussions have been posted on this vulnerability. |