|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Windows >> Novell Client Buffer Overflow Vulnerability Assessment Details
|
Novell Client Buffer Overflow |
||
|
Checks file version of dprpcw32.dll Detailed Explanation for this Vulnerability Assessment Summary : The remote Windows host contains a DLL that suffers from a buffer overflow flaw. Description : The file 'dprpcw32.dll' included with the Novell Client software reportedly contains a potential buffer overflow. See also : http://support.novell.com/cgi-bin/search/searchtid.cgi?/2973719.htm Solution : Install the 491psp2_dprpcw32.exe beta patch file referenced in the vendor advisory above. Network Security Threat Level: Critical / CVSS Base Score : 10.0 (AV:R/AC:L/Au:NR/C:C/I:C/A:C/B:N) Networks Security ID: 17931 Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Atari 800XL Computer with Chroma Added - Original Box - Tested and Working 100%
$225.00
Atari 800 Computer W/ Atari 810 Disk Drive Game Cartridge 100 Working Condition
$269.00
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
Vintage Atari 800XL ~ Home Computer in Original Box ~ Tested and Working
$149.90
Atari 400/800/XL/XE Computer SIO2PC - PC/Mac Disk Drive Emulator Adapter/Device
$15.25
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
$18.08
RARE San Jose Computer Special Edition 810 5 1/4" Floppy Disc Drive Atari 8-bit
$200.00
Lot Of 6 Vintage Atari Computing Magazines 1980's
$14.95
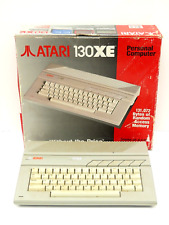
Atari 130XE Personal Retro Gaming Computer PC Complete in Original Box
$299.99
|
||
|
No Discussions have been posted on this vulnerability. |