|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gain root remotely >> Netware Perl CGI overflow Vulnerability Assessment Details
|
Netware Perl CGI overflow |
||
|
Too long URL kills Netware Perl handler Detailed Explanation for this Vulnerability Assessment The remote web server crashes when it receives a too long URL for the Perl handler. It might be possible to make it execute arbitrary code through this flaw. See http://support.novell.com/servlet/tidfinder/2966549 Network Security Threat Level: High Solution : Upgrade your web server. Networks Security ID: 8251 Vulnerability Assessment Copyright: This script is Copyright (C) 2003 Michel Arboi |
||
|
Cables, Connectors |

Samsung Galaxy Tab A8 10.5" SM-X200 128GB Wifi Only Tablet Open Box
$149.99
Samsung Galaxy Tab A 8.0" 2019 SM-T290 32GB WiFi Tablet Open Box
$94.99
SAMSUNG M393A2G40DB0-CPB 16GB PC4-17000P DDR4-2133 2RX4 ECC
$14.95
Samsung - S Pen Creator Edition - White
$40.00
Genuine Samsung Book Cover Keyboard for 14.6" Galaxy Tab S8 Ultra | S8 Ultra 5G
$89.99
Samsung Galaxy Tab A9 (X110) 64GB 4GB RAM International Version (New)
$129.99
Samsung Galaxy Chromebook Go, 14-inch, 32GB, Unlocked All Carriers - Silver
$99.95
Samsung 16GB 2Rx4 PC3-12800R M393B2G70BH0-CK0 DDR3 RDIMM - SERVER RAM
$8.90
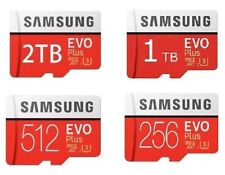
512GB SAMSUNG EVO Plus Micro SD MicroSDXC Flash Memory Card w/ SD Adapter
$21.99
Tempered Glass Screen Protector For Samsung Galaxy Tab S9/S9 FE/S9 Plus/S9 Ultra
$10.95
|
||
|
No Discussions have been posted on this vulnerability. |