|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Mono XSP Source Code Disclosure Vulnerability Vulnerability Assessment Details
|
Mono XSP Source Code Disclosure Vulnerability |
||
|
Tries to retrieve ASPX source code using XSP Detailed Explanation for this Vulnerability Assessment Summary : The remote web server is affected by an information disclosure vulnerability. Description : The remote host is running Mono XSP, a lightweight web server for hosting ASP.NET applications. The version of Mono XSP installed on the remote Windows host fails to properly validate filename extensions in URLs. A remote attacker may be able to leverage this issue to disclose the source of scripts hosted by the affected application using specially-crafted requests with URL-encoded space characters. See also : http://www.eazel.es/advisory007-mono-xsp-source-disclosure-vulnerability.html http://www.securityfocus.com/archive/1/454962/30/0/threaded http://www.mono-project.com/news/archive/2006/Dec-20.html Solution : Upgrade to Mono version 1.2.2 / 1.1.13.8.2 or later. Network Security Threat Level: Low / CVSS Base Score : 2.3 (AV:R/AC:L/Au:NR/C:P/I:N/A:N/B:N) Networks Security ID: 21687 Vulnerability Assessment Copyright: This script is Copyright (C) 2006-2007 Tenable Network Security |
||
|
Cables, Connectors |

Mellanox 10/25GbE SFP28 Network Card MCX512A-ACAT ConnectX-5 EN Ethernet Adapter
$284.00
Cisco SG110 24 Port Gigabit Ethernet Switch w/ 2 x SFP SG110-24
$117.00
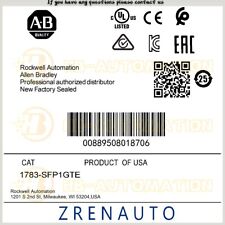
1783-SFP1GTE Allen Bradley 1G copper SFP #ZYPL
$679.87
F5 Networks 10GB OPT-0016-00 F5-UPG-SFP+-R 10GBASE/SR SFP Transceiver
$4.00
NEW Sealed Cisco SFP-10G-LR 10GBASE-LR SFP+ 1310nm 10km *US Shipping*
$18.00
Genuine Cisco SFP-10G-SR V03 10GBASE-SR SFP+ Transceiver Module 10-2415-03
$8.00
Mellanox Original MFM1T02A-SR 10GbE 10GBASE-SR SFP+ Transceiver
$9.00
10 PCS Cisco GLC-LH-SMD 10-2625-01 1310nm SFP Transceiver Module
$85.00
SFP-10G-SR V03 Original CISCO 10-2415-03 850nm 10GBASE-SR SFP+ Multi mode Module
$6.80
|
||
|
No Discussions have been posted on this vulnerability. |