|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Mambo Open Source Multiple Vulnerabilities Vulnerability Assessment Details
|
Mambo Open Source Multiple Vulnerabilities |
||
|
Tries to change mos_user_template cookie in Mambo Open Source Detailed Explanation for this Vulnerability Assessment Summary : The remote web server contains a PHP application that is affected by several issues. Description : The remote installation of Mambo Open Source fails to sanitize input to the 'mos_user_template' cookie before using it to include PHP code from a file. An unauthenticated attacker may be able to exploit this issue to view arbitrary files or to execute arbitrary PHP code on the affect host. In addition, the application suffers from a similar lack of sanitation of input to the 'username' parameter in the 'includes/mambo.php' script, the 'task' parameter in 'index2.php', and the 'filter' parameter in 'components/com_content/content.php' before using it in SQL statements. Provided PHP's 'magic_quotes_gpc' setting is disabled, a possible hacker can leverage these issues to manipulate database queries and, for example, log in as any user, including an admin. See also : http://www.gulftech.org/?node=research&article_id=00104-02242006 http://archives.neohapsis.com/archives/bugtraq/2006-02/0463.html http://www.nessus.org/u?12bf46b6 Solution : Apply the appropriate security patch listed in the vendor advisory above. Network Security Threat Level: High / CVSS Base Score : 8.0 (AV:R/AC:H/Au:NR/C:C/I:C/A:C/B:N) Networks Security ID: 16775 Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Cisco SG95-16 16-Port Gigabit Switch SG95-16-KR
$47.00
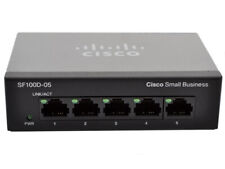
Cisco (SG100D-05-UK) 5-Ports External Ethernet Switch
$40.00
Cisco SG110 24 Port Gigabit Ethernet Switch w/ 2 x SFP SG110-24
$117.00
HP JG937A Flexnetwork 5130-48G PoE+ 48-Port Gigabit Network Switch
$65.95
NETGEAR JGS524 v2 ProSafe 24 Port Gigabit Ethernet Network Switch
$59.00
New Linksys SE3005 5-port Gigabit Ethernet Switch
$15.99
Linksys SE3008 8 Ports Rack Mountable Gigabit Ethernet Switch
$18.99
HP ProCurve 2530-24G J9776A 24 Port Gigabit Ethernet Managed Network Switch
$34.99
HP 2530-48G 48 Port Gigabit Ethernet Network Switch J9775A
$30.95
Cisco Catalyst WS-C3650-24PS-L 24-Port Gigabit Ethernet Network Switch TESTED
$49.99
|
||
|
No Discussions have been posted on this vulnerability. |