|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Mambo Code injection Vulnerability Vulnerability Assessment Details
|
Mambo Code injection Vulnerability |
||
|
Detect mambo code injection vuln Detailed Explanation for this Vulnerability Assessment Summary : The remote web server contains a PHP application that is affected by a remote file include vulnerability. Description : There is a flaw in the installed version of Mambo Open Source that may permit a possible hacker to execute arbitrary remote PHP code on this host because it fails to sanitize input to the 'mosConfig_absolute_path' of 'modules/mod_mainmenu.php' before using it to include PHP code from another file. Note that, for exploitation of this issue to be successful, PHP's 'register_globals' setting must be enabled. See also : http://archives.neohapsis.com/archives/bugtraq/2004-01/0141.html http://www.nessus.org/u?472f1d6d Solution : Upgrade to Mambo Open Source 4.5 Stable (1.0.2) or later. Network Security Threat Level: Medium / CVSS Base Score : 6 (AV:R/AC:H/Au:NR/C:P/A:P/I:P/B:N) Networks Security ID: 9445 Vulnerability Assessment Copyright: This script is Copyright (C) 2004-2006 Tenable Network Security |
||
|
Cables, Connectors |

Vintage Family owned Atari 1200xl computer sold as is tested turns on with cable
$299.99
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
Ms. Pac-Man Game Cartridge Atari TI99/4A TI-99/4A 1983 MS PACMAN UNTESTED/AS IS
$21.24
Vintage Atari 800XL ~ Home Computer in Original Box ~ Tested and Working
$149.90
Atari 1050 5.25" Floppy Disk Drive Tested (w/Power cables)
$99.99
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
RARE San Jose Computer Special Edition 810 5 1/4" Floppy Disc Drive Atari 8-bit
$195.00
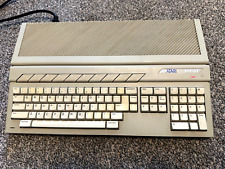
Vintage Atari 1040ST Computer Powers On
$165.00
Atari 600xl excellent condition - Video and RAM upgrades. 800XL compatible
$255.00
$225.00
|
||
|
No Discussions have been posted on this vulnerability. |