|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Windows >> ListManager with MSDE Weak sa Password Vulnerability Vulnerability Assessment Details
|
ListManager with MSDE Weak sa Password Vulnerability |
||
|
Checks for weak sa password vulnerability in ListManager with MSDE Detailed Explanation for this Vulnerability Assessment Summary : The remote database server uses a weak password for one of its administrative accounts. Description : The remote host appears to be running ListManager, a web-based commercial mailing list management application from Lyris. The version of ListManager on the remote host was installed using Microsoft SQL Server Desktop Engine (MSDE) for its database backend along with a weak password for the 'sa' account - 'lyris' followed by up to 5 digits. A possible hacker may be able to discover this password by means of a brute-force attack and gain administrative access to the database. See also : http://metasploit.com/research/vulns/lyris_listmanager/ http://archives.neohapsis.com/archives/fulldisclosure/2005-12/0349.html Solution : Assign a strong 'sa' password to MSDE and update the setting for '$sql_password' in ListManager's 'lmcfg.txt' file. Network Security Threat Level: Medium / CVSS Base Score : 4.2 (AV:R/AC:L/Au:R/C:P/I:P/A:P/B:N) Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
A8PicoCart Kit Atari XE XL unocart clone multicart cartridge game
$18.95
Vintage 1978 COMBAT ATARI Computer Game Cartridge in Original Box w Instructions
$19.50
Atari 600 XL Vintage Home Computer - New in Box, Unused
$200.00
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
ATARI XEGS Game System Tested Working CIB Complete in LATE CHILEAN RETAIL box
$590.00
Vintage Atari SX212 Modem w/Cable Untested
$29.14
Atari 400/800/XL/XE Computer SIO2PC - PC/Mac Disk Drive Emulator Adapter/Device
$15.25
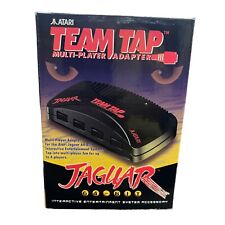
TEAM TAP Atari Jaguar Multi Player Adapter NEW In Box
$25.46
Atari 65xe nice condition (800xl compatible)
$225.00
|
||
|
No Discussions have been posted on this vulnerability. |