|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Land Down Under <= 800 Multiple Vulnerabilities Vulnerability Assessment Details
|
Land Down Under <= 800 Multiple Vulnerabilities |
||
|
Checks for SQL injection in LDU's index.php Detailed Explanation for this Vulnerability Assessment Summary : The remote web server contains a PHP script that permits SQL injection and cross-site scripting attacks. Description : The remote version of Land Down Under is prone to various SQL injection and cross-site scripting attacks provided PHP's 'magic_quotes' setting is disabled due to its failure to sanitize the request URI before using it in 'system/functions.php' in the function 'ldu_log()'. A malicious user may be able to exploit this issue to manipulate SQL queries, steal authentication cookies, and the like. In addition, it also fails to properly sanitize the user-supplied signature in forum posts.. A malicious user can exploit this vulnerability to steal authentication cookies and manipulate the HTML format in 'forums.php'. See also : http://www.securityfocus.org/archive/1/408664 http://www.neocrome.net/forums.php?m=posts&p=83412#83412 http://archives.neohapsis.com/archives/bugtraq/2005-08/0395.html Solution : Upgrade to Land Down Under version 801 or later. Network Security Threat Level: Medium / CVSS Base Score : 4 (AV:R/AC:H/Au:NR/C:P/A:N/I:P/B:N) Networks Security ID: 14618, 14619, 14677 Vulnerability Assessment Copyright: Copyright (C) 2005 Josh Zlatin-Amishav |
||
|
Cables, Connectors |

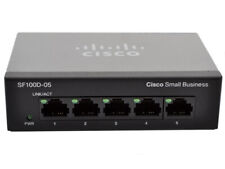
Cisco (SG100D-05-UK) 5-Ports External Ethernet Switch
$40.00
Cisco SG110 24 Port Gigabit Ethernet Switch w/ 2 x SFP SG110-24
$117.00
HP Procurve 2824 24 Gigabit Ports 10/100/1000 External Managed Switch J4903A
$74.99
New Linksys SE3005 5-port Gigabit Ethernet Switch
$18.99
New 10/100 Mbps 8 Ports Fast Ethernet LAN Desktop RJ45 Network Switch Hub
$11.49
Juniper Networks EX3300-48P 48-Port PoE+ 4x SFP+ Network Switch w/ Power Cord
$43.95
Netgear Prosafe GS724T V2 24-Port 10/100/1000 Gigabit Ethernet Network Switch
$27.99
Netgear ProSafe S3300-52X-POE+ 48-Port Gigabit PoE+ Stackable Network Switch
$100.95
Fortinet FortiSwitch FS-124D-POE 24 Port Gigabit Ethernet Switch UNREGISTERED
$99.97
|
||
|
No Discussions have been posted on this vulnerability. |