|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gain a shell remotely >> Kerio MailServer < 6.0.1 Vulnerability Assessment Details
|
Kerio MailServer < 6.0.1 |
||
|
Checks for Kerio MailServer < 6.0.1 Detailed Explanation for this Vulnerability Assessment The remote host is running a version of Kerio MailServer prior to 6.0.1. Kerio Mailserver is an SMTP server which ships with an embedded HTTP server. It has been reported that there are multiple remote overflows in versions of Kerio prior to 6.0.1, although the exact nature of these overflows is not yet known. *** NOTE: Nessus acertaind this vulnerability based on the received *** banner information from the host. If the host is running *** obfuscated banners, this may be a false positive. Solution : Upgrade to Kerio MailServer 6.0.1 or newer See also : http://www.securityfocus.com/bid/10936/ Network Security Threat Level: High Networks Security ID: 10936 Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

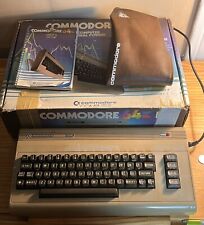
Commodore Vic 20 personal computer + box + power cords VINTAGE...FULL FUNCTION
$128.99
Commodore CM-141 Color Monitor Tested, Works RARE
$299.99
Apollo Vampire 600v2 / 600 V2 FPGA Accelerator Card for Commodore Amiga 600
$350.00
Vintage 1982 COMMODORE 64 Floppy Disk Drive MODEL VIC-1541 Original Box Works
$90.00
Commodore 1351 Mouse with Manual and Disk in Original Box Tested Working
$60.00
Commodore 64 LOT (Computer, Box, Adaptor, Manual, Cover) FOR PARTS OR REPAIR
$200.00
Commodore 64 C64 8 bit Home Computer Silver Label w/Power Supply KL
$224.99
Vintage Commodore MPS801 Matrix Printer W/ Manual
$51.00
pi1541 Disk Emulator for Commodore -
$38.95
1984 Commodore home Computer Video Color Monitor Model 1702
$275.00
|
||
|
No Discussions have been posted on this vulnerability. |