|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Peer-To-Peer File Sharing >> Kazaa is installed Vulnerability Assessment Details
|
Kazaa is installed |
||
|
Acertains if Kazaa is installed Detailed Explanation for this Vulnerability Assessment The remote host is using Kazaa - a p2p software, which may not be suitable for a business environment. Solution : Uninstall this software Network Security Threat Level: Low Networks Security ID: 4121, 4122, 5317, 6543, 6747 Vulnerability Assessment Copyright: This script is Copyright (C) 2003-2007 Tenable Network Security |
||
|
Cables, Connectors |

Vintage Apple Macintosh II 2 M5000 Computer no power very nice w drives card
$350.00
Vintage 1980s IBM PC Jr Model 4860 Desktop Tower Computer W/2 EXPANSIONS
$100.00
Vintage CARDCO Vic-20 C64 +4 C16 and C128 Parallel Printer Interface Card - QTY
$19.99
Computer Lab International 122 Key Vintage Keyboard PS/2 TESTED
$88.88
Vintage Apple Macintosh SE Case - Empty Shell - Housing retro project
$60.00
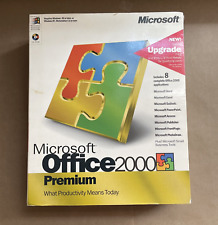
Vintage Microsoft Office 2000 Premium 4 CDs + Product Keys + Service Pack CD
$59.99
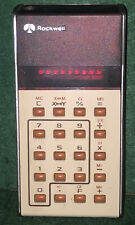
ROCKWELL SCIENTIFIC SLIDE RULE 31R CALCULATOR VINTAGE UNTESTED
$24.24
Vintage Cardco Vic-20, C64, C16, and C128 Parallel Printer Interface Card - New
$19.99
Vintage 1989 Macintosh Adobe Type Manager User Guide
$30.00
Vintage IBM Model F Mechanical Keyboard - Untested
$79.95
|
||
|
No Discussions have been posted on this vulnerability. |