|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Invision Power Board 2.x.x < 04-25-06 Multiple Vulnerabilities Vulnerability Assessment Details
|
Invision Power Board 2.x.x < 04-25-06 Multiple Vulnerabilities |
||
|
Checks for ck parameter SQL injection vulnerability in IPB Detailed Explanation for this Vulnerability Assessment Summary : The remote web server contains a PHP application that is susceptible to multiple types of attacks. Description : The installation of Invision Power Board on the remote host fails to sanitize input to the 'ck' parameter of the 'index.php' script before using it in database queries. An unauthenticated attacker may be able to leverage this issue to disclose sensitive information, modify data, or launch attacks against the underlying database. In addition, the application reportedly permits for execution of arbitrary PHP code contained in a posting due to a flaw in the 'search.php' script, remote file includes (requires admin capability), and cross-site scripting attacks using specially-crafted JPEG file. See also : http://www.securityfocus.com/archive/1/431990/30/0/threaded http://forums.invisionpower.com/index.php?showtopic=213374 Solution : Apply the IPB 2.x.x 04-25-06 Security Update referenced in the vendor URL above. Network Security Threat Level: Medium / CVSS Base Score : 5 (AV:R/AC:L/Au:NR/C:P/A:N/I:P/B:N) Networks Security ID: 17690, 17695 Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Intel Core i7-7800x CPU processor sr3nh 3.50ghz 6-Core 8.25mb lga-2066 X series
$37.29
Intel - Core i7-12700K Desktop Processor 12 (8P+4E) Cores up to 5.0 GHz Unloc...
$419.99
AMD Ryzen 9 5950X 16-core 32-thread Desktop Processor
$319.99
Intel - Core i9-12900K Desktop Processor 16 (8P+8E) Cores up to 5.2 GHz Unloc...
$619.99
Intel Core i5-6500 (SR2L6) @ 3.20GHz / 6MB / Socket 1151 / Skylake-S Processor
$23.99
Intel Core i7-6700 3.40 GHz QUAD Core (4 Core) Desktop Processor 8MB LGA 1151
$59.99
Intel Core i5-6500 3.2GHz 6MB SR2L6 / SR2BX Skt. FCLGA1151 Desktop Processor CPU
$24.50
Intel Core i7-6700 SR2L2 4.00 GHz LGA 1151 Quad-Core Processor
$58.00
Intel i7-8700 Coffee Lake 3.2GHz 6-Core Max Turbo 4.6GHz Processor
$49.01
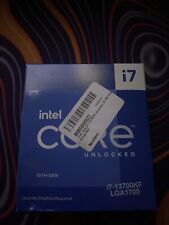
Intel Core i7-13700KF Processor (5.4 GHz, 16 Cores, LGA 1700) Box
$350.00
|
||
|
No Discussions have been posted on this vulnerability. |