|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> IceWarp Web Mail Multiple Flaws (4) Vulnerability Assessment Details
|
IceWarp Web Mail Multiple Flaws (4) |
||
|
Check the version of IceWarp WebMail Detailed Explanation for this Vulnerability Assessment Summary : It is possible to retrieve/delete local files on the remote system through the WebMail. Description : The remote host is running IceWarp Web Mail - a webmail solution available for the Microsoft Windows platform. The remote version of this software is vulnerable to a Directory Traversal vulnerability that may permit a possible hacker to retrieve arbitrary files on the system. Another input validation flaw permits to delete arbitrary files on the remote host. Note : this flaw indicates IceWarp is vulnerable to cross-site scripting attacks too. See also : http://marc.theaimsgroup.com/?l=bugtraq&m=112810385104168&w=2 Solution : None at this time. Network Security Threat Level: High / CVSS Base Score : 9 (AV:R/AC:L/Au:NR/C:C/A:P/I:C/B:N) Networks Security ID: 14988, 14986, 14980 Vulnerability Assessment Copyright: This script is Copyright (C) 2005-2007 Tenable Network Security |
||
|
Cables, Connectors |

A8PicoCart Kit Atari XE XL unocart clone multicart cartridge game
$18.95
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
Atari 600 XL Vintage Home Computer - New in Box, Unused
$200.00
ATARI XEGS Game System Tested Working CIB Complete in LATE CHILEAN RETAIL box
$590.00
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
Vintage Atari 800XL Computer With Original Box
$140.00
Atari 400/800/XL/XE Computer SIO2PC - PC/Mac Disk Drive Emulator Adapter/Device
$15.25
ATARI 1200XL Case Badges 400/800/815/830/822/800XL/600XL/800XE/xf551/1050/1090
$28.31
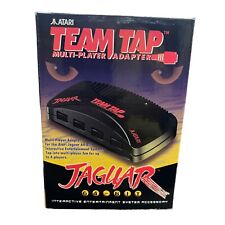
TEAM TAP Atari Jaguar Multi Player Adapter NEW In Box
$25.46
Atari 65xe nice condition (800xl compatible)
$225.00
|
||
|
No Discussions have been posted on this vulnerability. |