|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gain a shell remotely >> IMAP4buffer overflow in the BODY command Vulnerability Assessment Details
|
IMAP4buffer overflow in the BODY command |
||
|
checks for a buffer overflow in imapd Detailed Explanation for this Vulnerability Assessment Summary : It is possible to execute arbitrary code on the remote host, through the IMAP server. Description : The remote version of UW-IMAP is vulnerable to a buffer overflow condition which may permit an authenticated attacker to execute arbitrary code on the remote host with the rights of the IMAP server. Solution : Upgrade to imap-2001a Network Security Threat Level: Medium / CVSS Base Score : 6 (AV:R/AC:L/Au:R/C:C/A:C/I:C/B:N) Networks Security ID: 4713 Vulnerability Assessment Copyright: This script is Copyright (C) Tenable Network Security |
||
|
Cables, Connectors |

NEW Original OEM 60W Power Adapter Charger A1344 for APPLE 13" MacBook Pro A1278
$22.24
85W OEM NEW Power Adapter Charger For Apple Macbook Pro 13 15" A1424 A1502 A1398
$24.24
Original OEM 87W USB-C Power Adapter Charger for Apple MacBook Pro 15" 13" A1719
$28.44
OEM Apple MacBook Pro 13 A1706 A1708 2017 LCD Screen Display Assembly Silver
$140.99
Genuine Apple A1718 61W USB-C Power Adapter Apple OEM CHARGER
$24.99
OEM 61W USB C Type C Adapter Charger for Apple MacBook PRO 13" A1718 + Cable NEW
$23.00
Apple OEM Original (A1374) 45W MagSafe Power Adapter with Fold Plug Only - White
$10.95
APPLE OEM Original Cinema Display (Aluminum) Power Supply AC Adapter 65w or 90w
$13.99
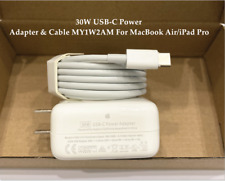
OEM 30W USB-C Power Adapter Charger for apple MacBook Air iPhone 11 12 Pro +Cord
$22.89
OEM 45W Charger Adapter Supply Power for Apple Macbook Air A1465 A1466 2012-2017
$8.99
|
||
|
No Discussions have been posted on this vulnerability. |