|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200701-03] Mozilla Thunderbird: Multiple vulnerabilities Vulnerability Assessment Details
|
[GLSA-200701-03] Mozilla Thunderbird: Multiple vulnerabilities |
||
|
Mozilla Thunderbird: Multiple vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200701-03 (Mozilla Thunderbird: Multiple vulnerabilities) Georgi Guninski and David Bienvenu discovered buffer overflows in the processing of long "Content-Type:" and long non-ASCII MIME headers. Additionally, Frederik Reiss discovered a heap-based buffer overflow in the conversion of a CSS cursor. Different vulnerabilities involving memory corruption in the browser engine were also fixed. Mozilla Thunderbird also contains less severe vulnerabilities involving JavaScript and Java. Impact A possible hacker could entice a user to view a specially crafted email that will trigger one of these vulnerabilities, possibly leading to the execution of arbitrary code. A possible hacker could also perform cross-site scripting attacks, leading to the exposure of sensitive information, like user credentials. Note that the execution of JavaScript or Java applets is disabled by default and enabling it is strongly discouraged. Workaround There are no known workarounds for all the issues at this time. References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-6497 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-6500 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-6501 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-6502 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-6503 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-6505 Solution: All Mozilla Thunderbird users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=mail-client/mozilla-thunderbird-1.5.0.9" All Mozilla Thunderbird binary release users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=mail-client/mozilla-thunderbird-bin-1.5.0.9" Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: (C) 2007 Michel Arboi |
||
|
Cables, Connectors |

ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
Asus H81M-C Intel LGA1150 DDR3 Desktop Motherboard MicroATX Socket H3
$24.99
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
Asrock Z390 Phantom Gaming 4S/AC Wifi 8th/9th Gen Intel 1151 Motherboard Bulk
$47.55
ASUS Prime Z390-A LGA 1151 Intel Z390 SATA USB 3.1 ATX Motherboard NO I/O
$99.00
MSI B450M PRO-VDH MAX AM4 AMD B450 USB3.2 Micro-ATX Motherboard
$67.99
ASUS Prime Q270M-C LGA1151 DP HDMI VGA SATA 6GB/s USB 3.0 MicroATX Motherboard
$34.19
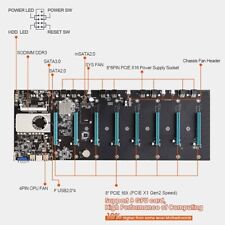
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
GIGABYTE MB10-Datto Motherboard Xeon D-1521- SR2DF 2.40 GHz- Open Box
$121.50
|
||
|
No Discussions have been posted on this vulnerability. |