|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200612-06] Mozilla Thunderbird: Multiple vulnerabilities Vulnerability Assessment Details
|
[GLSA-200612-06] Mozilla Thunderbird: Multiple vulnerabilities |
||
|
Mozilla Thunderbird: Multiple vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200612-06 (Mozilla Thunderbird: Multiple vulnerabilities) It has been identified that Mozilla Thunderbird improperly handles Script objects while they are being executed, permiting them to be modified during execution. JavaScript is disabled in Mozilla Thunderbird by default. Mozilla Thunderbird has also been found to be vulnerable to various potential buffer overflows. Lastly, the binary release of Mozilla Thunderbird is vulnerable to a low exponent RSA signature forgery issue because it is bundled with a vulnerable version of NSS. Impact A possible hacker could entice a user to view a specially crafted email that causes a buffer overflow and again executes arbitrary code or causes a Denial of Service. A possible hacker could also entice a user to view an email containing specially crafted JavaScript and execute arbitrary code with the rights of the user running Mozilla Thunderbird. It is important to note that JavaScript is off by default in Mozilla Thunderbird, and enabling it is strongly discouraged. It is also possible for a possible hacker to create SSL/TLS or email certificates that would not be detected as invalid by the binary release of Mozilla Thunderbird, raising the possibility for Man-in-the-Middle attacks. Workaround There is no known workaround at this time. References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-5462 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-5463 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-5464 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-5747 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-5748 https://bugzilla.mozilla.org/show_bug.cgi?id=360409 Solution: Users upgrading to the following releases of Mozilla Thunderbird should note that this version of Mozilla Thunderbird has been found to not display certain messages in some cases. All Mozilla Thunderbird users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=mail-client/mozilla-thunderbird-1.5.0.8" All Mozilla Thunderbird binary release users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=mail-client/mozilla-thunderbird-bin-1.5.0.8" Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: (C) 2006 Michel Arboi |
||
|
Cables, Connectors |

Mini External OLED AMIGA Gotek Floppy Drive Emulator For Amiga 500/500+/600/1200
$37.24
Amiga A500 NTSC, 1 MB Chip RAM, HDMI, Wireless Mouse
$360.00
AMIGA 2000 Mainboard Rev 6 ASIS
$100.00
Commodore Amiga 2000 2000HD 2500 keyboard (KKQ-E96YC) . Fully working
$219.00
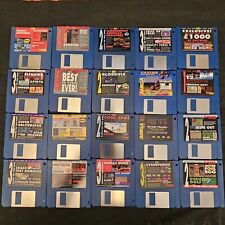
Amiga 3.5'' Floppy Disk Games/Demo Games Bundle 70 total new not tested
$80.47
Amiga Textcraft Plus, Amiga Extras + GEOS, more, Eleven 3.5" Floppy Disk Lot
$19.25
Amiga 500 Gotek Custom Mount USB Floppy Emulator - Complete Kit with Gotek
$65.00
Vampirized Video Toaster Branded Amiga 2000 Desktop Computer w/Flyer Vampire etc
$4999.98
TeensyROM Cartridge for Commodore 64/128: MIDI, Fastload, Emulation, and Network
$65.00
Amiga Gotek V3.42 External Ivory & BIEGE + 0.96 OLED + Rotary with DF1/ 23p Lead
$88.58
|
||
|
No Discussions have been posted on this vulnerability. |