|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200608-22] fbida: Arbitrary command execution Vulnerability Assessment Details
|
[GLSA-200608-22] fbida: Arbitrary command execution |
||
|
fbida: Arbitrary command execution Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200608-22 (fbida: Arbitrary command execution) Toth Andras has discovered a typographic mistake in the "fbgs" script, shipped with fbida if the "fbcon" and "pdf" USE flags are both enabled. This script runs "gs" without the -dSAFER option, thus permiting a PostScript file to execute, delete or create any kind of file on the system. Impact A remote attacker can entice a vulnerable user to view a malicious PostScript or PDF file with fbgs, which may result with the execution of arbitrary code. Workaround There is no known workaround at this time. References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-3119 Solution: All fbida users with the "fbcon" and "pdf" USE flags both enabled should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=media-gfx/fbida-2.03-r4" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2006 Michel Arboi |
||
|
Cables, Connectors |

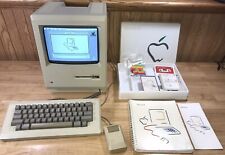
Macintosh Platinum Mouse - Apple 128K 512K 512Ke Mac Plus Lisa IIe M0100 - NEW
$44.99
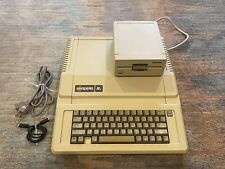
Apple IIe Computer - 128k Enhanced w/ 80col + 5.25 Drive Card + Serial Card
$349.00
Vintage Apple lle 128k Enhanced Computer A2S2064 Rebuilt W/ Disk Drive & more
$389.99
Apple Macintosh 128k 512k Plus Analog Board Capacitor Re-Cap Kit - US Shipping
$23.95
1984 APPLE MACINTOSH Model M0001 1st MAC 128K 40th Anniversary PICASSO KIT NICE
$4999.99
Apple Macintosh 128K M0001 Computer with 128K Label - Estate Sale SOLD AS IS
$2468.10
Apple Macintosh Mac 128K M0001 Computer 1984 w/Keyboard M0110 Mouse M0100 & Bag
$849.99
Vintage M0001 Macintosh 128 128K Computer 1984 Front Cover Nice
$79.00
Apple Macintosh 128K Parts Kit - P/N 073-0140-A
$273.60
Apple Macintosh 128K M0001 Computer with Mouse, no keyboard. Case included. 1984
$507.01
|
||
|
No Discussions have been posted on this vulnerability. |