|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200604-05] Doomsday: Format string vulnerability Vulnerability Assessment Details
|
[GLSA-200604-05] Doomsday: Format string vulnerability |
||
|
Doomsday: Format string vulnerability Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200604-05 (Doomsday: Format string vulnerability) Luigi Auriemma discovered that Doomsday incorrectly implements formatted printing. Impact A remote attacker could exploit these vulnerabilities to execute arbitrary code with the rights of the user running the Doomsday server or client by sending specially crafted strings. Workaround There is no known workaround at this time. References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-1618 http://aluigi.altervista.org/adv/doomsdayfs-adv.txt Solution: Doomsday has been masked in Portage pending the resolution of these issues. All Doomsday users are advised to uninstall the package until further notice. # emerge --ask --verbose --unmerge games-fps/doomsday Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: (C) 2006 Michel Arboi |
||
|
Cables, Connectors |

Commodore Amiga A2386SX Bridge board
$900.00
Amiga Aminet 10 February 96 1996 Commodore
$13.20
Mini External OLED AMIGA Gotek Floppy Drive Emulator For Amiga 500/500+/600/1200
$39.20
Brand New Amiga 4000T Keyboard
$299.99
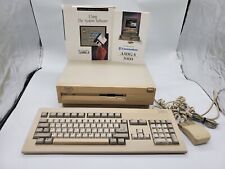
Commodore Amiga 3000 030 25Mhz + Keyboard + Mouse - Amiga OS 3.2 - WORKS 100%
$1599.99
Amiga 500 Gotek Custom Mount USB Floppy Emulator - Complete Kit with Gotek
$65.00
Apollo Vampire 600v2 / 600 V2 FPGA Accelerator Card for Commodore Amiga 600
$350.00
Commodore Amiga 1060 Side Car Expansion "IBM PC EMULATOR" VERY RARE COLLECTIBLE
$1499.95
AMIGA 500 COMPUTER COMMODORE Complete in Box Powers/untested Good Condition
$370.00
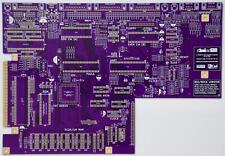
Raemixx500 Commodore Amiga500+ V2 Remake PCB Gold Plated
$35.15
|
||
|
No Discussions have been posted on this vulnerability. |