|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200508-07] AWStats: Arbitrary code execution using malicious Referrer information Vulnerability Assessment Details
|
[GLSA-200508-07] AWStats: Arbitrary code execution using malicious Referrer information |
||
|
AWStats: Arbitrary code execution using malicious Referrer information Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200508-07 (AWStats: Arbitrary code execution using malicious Referrer information) When using a URLPlugin, AWStats fails to sanitize Referrer URL data before using them in a Perl eval() routine. Impact A remote attacker can include arbitrary Referrer information in a HTTP request to a web server, therefore injecting tainted data in the log files. When AWStats is run on this log file, this can result in the execution of arbitrary Perl code with the rights of the user running AWStats. Workaround Disable all URLPlugins in the AWStats configuration. References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-1527 http://www.idefense.com/application/poi/display?id=290&type=vulnerabilities Solution: All AWStats users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=net-www/awstats-6.5" Note: Users with the vhosts USE flag set should manually use webapp-config to finalize the update. Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Apple Mac Powerbook Duo 230 Vintage Laptop
$60.00
Vintage Dream Writer NTS 325 Computer Basic Language Notebook “Untested “
$30.00
Vintage Compaq 141649-004 2 Button PS/2 Gray Mouse M-S34 - FAST SHIPPING - NEW
$8.99
Datacomp DCK 84 BRAND NEW Vintage Keyboard
$39.00
Vintage Classic Apple Macintosh System Boot Install Disk Floppy/CD *Pick Version
$10.39
Vintage Apple LisaDraw Brochure, very nice condition
$40.00
Voltage Blaster (Enhanced) -5V ISA AT ATX Power for Vintage Retro PCs US Seller
$12.95
NEW Manufacture OLD STYLE Oval 3 Prong Power Cord HP style 125V 7A 875W Vintage
$39.95
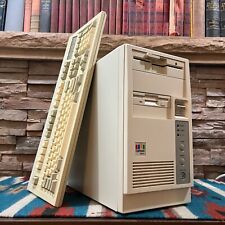
Vintage Retro AT PC Tower - Intel 486 4MB 3.5" 5.25" OPL Sound Keyboard POSTS
$199.00
Vintage Tandy (MMS-10) Amplified Speaker System W/ Original Box & Cords
$88.67
|
||
|
No Discussions have been posted on this vulnerability. |