|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200507-20] Shorewall: Security policy bypass Vulnerability Assessment Details
|
[GLSA-200507-20] Shorewall: Security policy bypass |
||
|
Shorewall: Security policy bypass Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200507-20 (Shorewall: Security policy bypass) Shorewall fails to enforce security policies if configured with "MACLIST_DISPOSITION" set to "ACCEPT" or "MACLIST_TTL" set to a value greater or equal to 0. Impact A client authenticated by MAC address filtering could bypass all security policies, possibly permiting him to gain access to restricted services. Workaround Set "MACLIST_TTL" to "0" and "MACLIST_DISPOSITION" to "REJECT" in the Shorewall configuration file (usually /etc/shorewall/shorewall.conf). References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-2317 http://www.shorewall.net/News.htm#20050717 Solution: All Shorewall users should upgrade to the latest available version: # emerge --sync # emerge --ask --oneshot --verbose net-firewall/shorewall Network Security Threat Level: Low Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Bare S100 CPU Replacement for ALTAIR 8800 IMSAI 8080 JAIR Single Board Computer
$42.00
MITS ALTAIR 8800 Original Vintage Microcomputer
$6000.00
MITS ALTAIR 8800 88-2SIO S-100 Reproduction Board
$35.00
MITS Altair 8800 Computer Bamboo Reproduction Arduino Tested Working Assembled
$649.99
MITS ALTAIR 8800 Original Vintage Microcomputer S-100 Buy It Now $5999
$5999.00
MITS ALTAIR 8800 Original Vintage Microcomputer with 14 boards - Buy It Now
$9500.00
1974 Early Microcomputers by MITS Altair 8800's Ed Roberts HP-9810 Mark-8 Scelbi
$55.00
Altair MITS 8800 CPU Card 8080A S-100 S100 replica IMSAI CP/M
$35.00
Vintage Altair 8088 CPU Wire Wrapped S100 Card w Mon EPROM circuit board #T71
$99.00
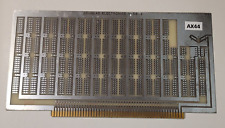
Altair MSAI Douglas Electronics 11 DE Prototype Card S100 circuit board #AX44
$69.00
|
||
|
No Discussions have been posted on this vulnerability. |