|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200505-02] Oops!: Remote code execution Vulnerability Assessment Details
|
[GLSA-200505-02] Oops!: Remote code execution |
||
|
Oops!: Remote code execution Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200505-02 (Oops!: Remote code execution) A format string flaw has been detected in the my_xlog() function of the Oops! proxy, which is called by the passwd_mysql and passwd_pgsql module's auth() functions. Impact A remote attacker could send a specially crafted HTTP request to the Oops! proxy, potentially triggering this vulnerability and leading to the execution of arbitrary code. Workaround There is no known workaround at this time. References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-1121 Solution: All Oops! users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=net-proxy/oops-1.5.24_pre20050503" Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Cisco ASA 5520 Adaptive Security Appliance
$56.75
Fortinet FortiGate-40C Network Security Firewall
$42.50
Fortinet Fortigate FG-61E | Firewall Network Security Appliance
$49.99
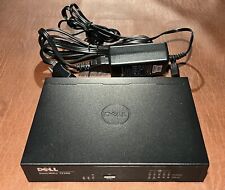
Dell SonicWall TZ300 5-Port Network Security Firewall Appliance APL28-0B4
$24.95
Fortinet FortiGate FG-40F Network Security Firewall
$100.00
OPNsense six-port Gigabit router/firewall on Lanner FW-7535 hardware
$69.00
Palo Alto PA-220 Next-Gen Firewall 520-000309-00J w/ Power adapter
$69.98
Fortinet Fortiwifi 60D FG-60D Security Appliance Firewall / VPN w/ AC Adapter
$999.97
Dell SonicWALL TZ300 | Firewall Security Appliance
$24.99
|
||
|
No Discussions have been posted on this vulnerability. |