|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200503-10] Mozilla Firefox: Various vulnerabilities Vulnerability Assessment Details
|
[GLSA-200503-10] Mozilla Firefox: Various vulnerabilities |
||
|
Mozilla Firefox: Various vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200503-10 (Mozilla Firefox: Various vulnerabilities) Impact By setting up malicious websites and convincing users to follow untrusted links or obey very specific drag-and-drop or download instructions, attackers may leverage the various spoofing issues to fake other websites to get access to confidential information, push users to download malicious files or make them interact with their browser preferences. The temporary directory issue permits local attackers to overwrite arbitrary files with the rights of another local user. The overflow issues, while not thought to be exploitable, may permit a malicious downloaded page to execute arbitrary code with the rights of the user viewing the page. Workaround There is no known workaround at this time. References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2004-1156 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0230 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0231 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0232 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0233 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0255 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0527 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0578 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0584 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0585 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0586 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0588 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0589 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0590 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0591 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0592 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0593 http://www.mozilla.org/projects/security/known-vulnerabilities.html Solution: All Firefox users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=net-www/mozilla-firefox-1.0.1" All Firefox binary users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=net-www/mozilla-firefox-bin-1.0.1" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

NetFu Firewall 1U, Intel CPU, 8 x Gigabit, SFP, w/ pfSense, Others, NEW OPTIONS
$580.84
NEW NetFu Firewall Mini, Intel CPU, 6 Port Gigabit, w/ pfSense, others
$336.00
Cisco ASA5525-FTD-K9 Security Appliance with FirePower Services
$1000.00
Fortinet Fortigate FG-61E | Firewall Network Security Appliance
$49.99
Fortinet FortiGate FG-40F Network Security Firewall
$100.00
OPNsense six-port Gigabit router/firewall on Lanner FW-7535 hardware
$69.00
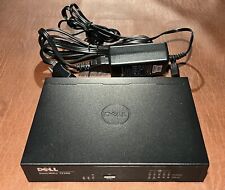
Dell SonicWall TZ300 5-Port Network Security Firewall Appliance APL28-0B4
$24.95
Dell SonicWALL TZ300 | Firewall Security Appliance
$24.99
Fortinet Fortiwifi 60D FG-60D Security Appliance Firewall / VPN w/ AC Adapter
$999.97
FORTINET FORTIGATE 40F Next GEN Firewall Security Unregistered (FG-40F)-Open Box
$214.99
|
||
|
No Discussions have been posted on this vulnerability. |