|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200501-42] VDR: Arbitrary file overwriting issue Vulnerability Assessment Details
|
[GLSA-200501-42] VDR: Arbitrary file overwriting issue |
||
|
VDR: Arbitrary file overwriting issue Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200501-42 (VDR: Arbitrary file overwriting issue) Javier Fernandez-Sanguino Pena from the Debian Security Audit Team discovered that VDR accesses user-controlled files insecurely. Impact A local attacker could create malicious links and invoke a VDR recording that would overwrite arbitrary files on the system. Workaround There is no known workaround at this time. References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0071 Solution: All VDR users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose ">=media-video/vdr-1.2.6-r1" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Cisco SG110 24 Port Gigabit Ethernet Switch w/ 2 x SFP SG110-24
$117.00
Mellanox 10/25GbE SFP28 Network Card MCX512A-ACAT ConnectX-5 EN Ethernet Adapter
$284.00
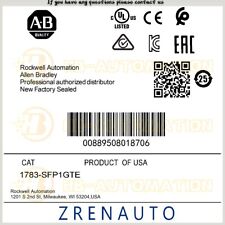
1783-SFP1GTE Allen Bradley 1G copper SFP #ZYPL
$879.87
Cisco 110 24 Port 10/100 Ethernet Switch with 2 x SFP SF112-24-NA
$90.00
NEW Sealed Cisco SFP-10G-LR 10GBASE-LR SFP+ 1310nm 10km *US Shipping*
$18.00
F5 Networks 10GB OPT-0016-00 F5-UPG-SFP+-R 10GBASE/SR SFP Transceiver
$4.00
Genuine Cisco SFP-10G-SR V03 10GBASE-SR SFP+ Transceiver Module 10-2415-03
$8.00
Mellanox Original MFM1T02A-SR 10GbE 10GBASE-SR SFP+ Transceiver
$9.00
10 PCS Cisco GLC-LH-SMD 10-2625-01 1310nm SFP Transceiver Module
$85.00
LOT OF 20 Genuine Cisco SFP-10G-SR V03 10GBASE-SR SFP+ Transceiver Module
$89.00
|
||
|
No Discussions have been posted on this vulnerability. |