|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200501-22] poppassd_pam: Unauthorized password changing Vulnerability Assessment Details
|
[GLSA-200501-22] poppassd_pam: Unauthorized password changing |
||
|
poppassd_pam: Unauthorized password changing Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200501-22 (poppassd_pam: Unauthorized password changing) Gentoo Linux developer Marcus Hanwell discovered that poppassd_pam did not check that the old password was valid before changing passwords. Our investigation revealed that poppassd_pam did not call pam_authenticate before calling pam_chauthtok. Impact A remote attacker could change the system password of any user, including root. This leads to a complete compromise of the POP accounts, and may also lead to a complete root compromise of the affected server, if it also provides shell access authenticated using system passwords. Workaround There is no known workaround at this time. References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2005-0002 Solution: All poppassd_pam users should migrate to the new package called poppassd_ceti: # emerge --sync # emerge --ask --oneshot --verbose ">=net-mail/poppassd_ceti-1.8.4" Note: Portage will automatically replace the poppassd_pam package by the poppassd_ceti package. Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

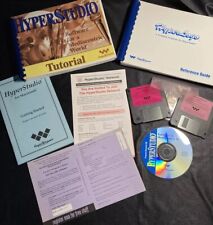
Vintage Lot of Hyperstudio by Roger Wagner -- Bundle of Software and Books
$35.00
Vintage Compaq Presario V410 Color Monitor w/Stand Retro Cables Original Box
$50.00
Vintage Sprint Logo Black Computer Briefcase Bag
$12.95
Matched Pair Vintage Rare Sun 370-2162 SM151, 150MHz Ross HyperSPARC MBUS Module
$399.98
Microsoft MSDN Library Office 2000 Developer 3 Discs CD 1999 NT 98 Vtg w/Case
$11.99
Intel Celeron 300 333 MHz SL2YP SL2X8 SL2WN SL2WN SL2Y2 vintage CPU GOLD
$10.95
Vintage AST Ascentia 900N 4/50 CS10 Notebook UNTESTED no cables
$29.99
Vintage Passport MIDI Interface For Macintosh Mac Apple
$20.00
$150.00
IBM PCjr 4860 JR Vintage PC Desktop Computer W/ Power Cord & Keyboard, *READ
$154.99
|
||
|
No Discussions have been posted on this vulnerability. |