|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200409-30] xine-lib: Multiple vulnerabilities Vulnerability Assessment Details
|
[GLSA-200409-30] xine-lib: Multiple vulnerabilities |
||
|
xine-lib: Multiple vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200409-30 (xine-lib: Multiple vulnerabilities) xine-lib contains two stack-based overflows and one heap-based overflow. In the code reading VCD disc labels, the ISO disc label is copied into an unprotected stack buffer of fixed size. Also, there is a buffer overflow in the code that parses subtitles and prepares them for display (XSA-2004-4). Finally, xine-lib contains a heap-based overflow in the DVD sub-picture decoder (XSA-2004-5). (Please note that the VCD MRL issue mentioned in XSA-2004-4 was fixed with GLSA 200408-18.) Impact With carefully-crafted VCDs, DVDs, MPEGs or subtitles, a possible hacker may cause xine-lib to execute arbitrary code with the permissions of the user. Workaround There is no known workaround at this time. References: http://www.securityfocus.com/archive/1/375485/2004-09-02/2004-09-08/0 http://www.securityfocus.com/archive/1/375482/2004-09-02/2004-09-08/0 Solution: All xine-lib users should upgrade to the latest version: # emerge sync # emerge -pv ">=media-libs/xine-lib-1_rc6" # emerge ">=media-libs/xine-lib-1_rc6" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

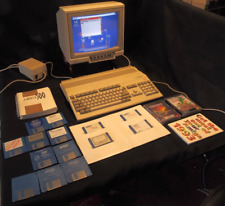
Mini External OLED AMIGA Gotek Floppy Drive Emulator For Amiga 500/500+/600/1200
$37.24
Amiga 500 Gotek Custom Mount USB Floppy Emulator - Complete Kit with Gotek
$65.00
Amiga MiniMig 2.0 - FPGA Amiga 500 with real 68000CPU
$179.99
Commodore Amiga CD32 Power Supply 100v-240v NEW
$38.00
Commodore Amiga 500 with Original Box. Power Supply Games and More 1 MEG No.2
$463.19
$299.95
AT&T Card w/ Motorola 060 XC68060RC50A 68060 & Seagate ST51080N SCSI2 Hard Drive
$324.95
Apollo Vampire 600v2 / 600 V2 FPGA Accelerator Card for Commodore Amiga 600
$350.00
AMIGA 500 COMPUTER COMMODORE Complete in Box Powers/untested Good Condition
$370.00
Amiga 5.25 External DUAL SLIM Floppy Disk Drive VERY RARE
$199.00
|
||
|
No Discussions have been posted on this vulnerability. |