|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200408-22] Mozilla, Firefox, Thunderbird, Galeon, Epiphany: New releases fix vulnerabilities Vulnerability Assessment Details
|
[GLSA-200408-22] Mozilla, Firefox, Thunderbird, Galeon, Epiphany: New releases fix vulnerabilities |
||
|
Mozilla, Firefox, Thunderbird, Galeon, Epiphany: New releases fix vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200408-22 (Mozilla, Firefox, Thunderbird, Galeon, Epiphany: New releases fix vulnerabilities) Mozilla, Galeon, Epiphany, Mozilla Firefox and Mozilla Thunderbird contain the following vulnerabilities: All Mozilla tools use libpng for graphics. This library contains a buffer overflow which may lead to arbitrary code execution. If a user imports a forged Certificate Authority (CA) certificate, it may overwrite and corrupt the valid CA already installed on the machine. Mozilla, Mozilla Firefox, and other gecko-based browsers also contain a bug in their caching which may permit the SSL icon to remain visible, even when the site in question is an insecure site. Impact Users of Mozilla, Mozilla Firefox, and other gecko-based browsers are susceptible to SSL certificate spoofing, a Denial of Service against legitimate SSL sites, crashes, and arbitrary code execution. Users of Mozilla Thunderbird are susceptible to crashes and arbitrary code execution via malicious e-mails. Workaround There is no known workaround for most of these vulnerabilities. All users are advised to upgrade to the latest available version. References: http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2004-0763 http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2004-0758 http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2004-0597 http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2004-0598 http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2004-0599 Solution: All users should upgrade to the latest stable version: # emerge sync # emerge -pv your-version # emerge your-version Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Cisco ASA 5520 Adaptive Security Appliance
$56.75
Check Point L-71 6 Port Gigabit Enterprise Firewall
$34.99
Fortinet FortiGate-40C Network Security Firewall
$42.50
Fortinet Fortigate FG-61E | Firewall Network Security Appliance
$49.99
Fortinet FortiGate FG-40F Network Security Firewall
$100.00
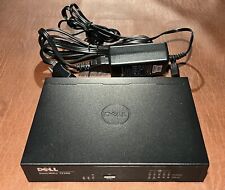
Dell SonicWall TZ300 5-Port Network Security Firewall Appliance APL28-0B4
$24.95
OPNsense six-port Gigabit router/firewall on Lanner FW-7535 hardware
$69.00
Palo Alto PA-220 Next-Gen Firewall 520-000309-00J w/ Power adapter
$69.98
Fortinet Fortiwifi 60D FG-60D Security Appliance Firewall / VPN w/ AC Adapter
$999.97
Dell SonicWALL TZ300 | Firewall Security Appliance
$24.99
|
||
|
No Discussions have been posted on this vulnerability. |