|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200405-22] Apache 1.3: Multiple vulnerabilities Vulnerability Assessment Details
|
[GLSA-200405-22] Apache 1.3: Multiple vulnerabilities |
||
|
Apache 1.3: Multiple vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200405-22 (Apache 1.3: Multiple vulnerabilities) On 64-bit big-endian platforms, mod_access does not properly parse Allow/Deny rules using IP addresses without a netmask which could result in failure to match certain IP addresses. Terminal escape sequences are not filtered from error logs. This could be used by a possible hacker to insert escape sequences into a terminal emulater vulnerable to escape sequences. mod_digest does not properly verify the nonce of a client response by using a AuthNonce secret. This could permit a possible hacker to replay the response of another website. This does not affect mod_auth_digest. On certain platforms there is a starvation issue where listening sockets fails to handle short-lived connection on a rarely-accessed listening socket. This causes the child to hold the accept mutex and block out new connections until another connection arrives on the same rarely-accessed listening socket thus leading to a denial of service. Impact These vulnerabilities could lead to attackers bypassing intended access restrictions, denial of service, and possibly execution of arbitrary code. Workaround There is no known workaround at this time. References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-0993 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-0020 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-0987 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2004-0174 Solution: All users should upgrade to the latest stable version of Apache 1.3. # emerge sync # emerge -pv ">=net-www/apache-1.3.31" # emerge ">=net-www/apache-1.3.31" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

VINTAGE DEC Digital RK11-D DISK CONTROL M7255 PDP 11 (B1)
$129.99
Vintage DEC/CLEARPOINT INC. -QRAM-2 SAB-1 1MB Q-BUS MEMORY MSV11-QA (B2)
$129.99
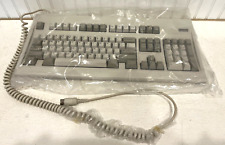
Digital Equipment Corporation DEC-2000 Vintage Keyboard - NOS NEW in Plastic
$129.95
DEC PDP 8/M PDP 8M / 4 avail / Vintage Digital Equipment Corp /Also DEC PDP 12
$5775.00
Vintage DEC Digital RX 180 AB Dual 5.25" Disk Drive
$149.00
Vintage Digital DEC dfo1 Acoustic Coupler modem Anderson Jacobsen Mod# A242 RARE
$195.95
Rare Vintage DEC DIGITAL DFO3 modem with manual Powers up but UNTESTED
$69.95
DEC DIGITAL Equipment Corp VT220-D2 Vintage CRT Terminal
$215.00
Vintage DEC Digital M8048 5013995C PDP-11 LSI 11 ROM (B3)
$79.99
Vintage DEC/The Redac mini cabinet front panel Digital Equipment Corp. 19"
$269.99
|
||
|
No Discussions have been posted on this vulnerability. |