|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gentoo Local Security Checks >> [GLSA-200404-13] CVS Server and Client Vulnerabilities Vulnerability Assessment Details
|
[GLSA-200404-13] CVS Server and Client Vulnerabilities |
||
|
CVS Server and Client Vulnerabilities Detailed Explanation for this Vulnerability Assessment The remote host is affected by the vulnerability described in GLSA-200404-13 (CVS Server and Client Vulnerabilities) There are two vulnerabilities in CVS one in the server and one in the client. The server vulnerability permits a malicious client to request the contents of any RCS file to which the server has permission, even those not located under $CVSROOT. The client vulnerability permits a malicious server to overwrite files on the client machine anywhere the client has permissions. Impact Arbitrary files may be read or written on CVS clients and servers by anybody with access to the CVS tree. Workaround There is no known workaround at this time. All users are encouraged to upgrade to the latest stable version of CVS. References: http://ccvs.cvshome.org/source/browse/ccvs/NEWS?rev=1.116.2.92&content-type=text/x-cvsweb-markup Solution: All CVS users should upgrade to the latest stable version. # emerge sync # emerge -pv ">=dev-util/cvs-1.11.15" # emerge ">=dev-util/cvs-1.11.15" Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Samsung Galaxy Tab A8 10.5" SM-X200 128GB Wifi Only Tablet Open Box
$149.99
Samsung Galaxy Tab A 8.0" 2019 SM-T290 32GB WiFi Tablet Open Box
$94.99
Samsung Galaxy Tab S2 9.7-Inch - 32GB - Wi-Fi Gold - SM-T813NZDEXAR
$44.99
Samsung Galaxy Tab A9 (X110) 64GB 4GB RAM International Version (New)
$129.99
Genuine Samsung Book Cover Keyboard for 14.6" Galaxy Tab S8 Ultra | S8 Ultra 5G
$89.99
Samsung Galaxy Chromebook Go, 14-inch, 32GB, Unlocked All Carriers - Silver
$99.95
Samsung - S Pen Creator Edition - White
$40.00
Samsung Galaxy Tab S7 SM-T878U 128GB, Wi-Fi + 5G (T-Mobile), 11" (Parts Only)
$129.13
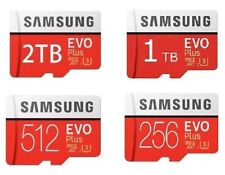
512GB SAMSUNG EVO Plus Micro SD MicroSDXC Flash Memory Card w/ SD Adapter
$21.99
Tempered Glass Screen Protector For Samsung Galaxy Tab S9/S9 FE/S9 Plus/S9 Ultra
$10.95
|
||
|
No Discussions have been posted on this vulnerability. |