|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> FreeBSD Local Security Checks >> FreeBSD : fetchmail -- fetchmailconf local password exposure (737) Vulnerability Assessment Details
|
FreeBSD : fetchmail -- fetchmailconf local password exposure (737) |
||
|
Check for fetchmail Detailed Explanation for this Vulnerability Assessment The remote host is missing an update to the system The following package is affected: fetchmail Solution : Update the package on the remote host See also : Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Extron RGB-160XI Analog Computer Video 60-378-01
$187.06
The analog thing modern open source, educational, low-cost analog computer
$800.00
Vintage 1960s Donner Model 3000 Analog Computer ~ MUSEUM PIECE Extremely Rare
$4000.00
NEW Aquarius+ Computer Signature Edition - 8Bit Retro System
$229.00
Apple Macintosh SE/30 M5119 Computer 8MB RAM Recapped Working *See Description*
$475.00
Apple IIc Analog Board NOS - 661-0265
$74.00
IBM Modem Saver Phone Line Tester
$7.99
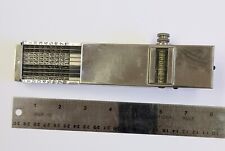
Landen Computer. Circa 1898. the Rapid Computer Company. With Original Case.
$425.00
ACASIS PCIE Capture Card HDMI 1.4 1080P60HZ PCIE 2.0 X4 20Gbps for Video Capture
$248.99
MultiTech FaxFinder FF240 Windows Fax Server SKU92500751LF Analog 1N22860#3
$139.49
|
||
|
No Discussions have been posted on this vulnerability. |