|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Fedora Local Security Checks >> Fedora Core 4 2006-580: dia Vulnerability Assessment Details
|
Fedora Core 4 2006-580: dia |
||
|
Check for the version of the dia package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory FEDORA-2006-580 (dia). The Dia drawing program is designed to be like the Windows(TM) Visio program. Dia can be used to draw different types of diagrams, and includes support for UML static structure diagrams (class diagrams), entity relationship modeling, and network diagrams. Dia can load and save diagrams to a custom file format, can load and save in .xml format, and can export to PostScript(TM). Update Information: CVE-2006-2480/CVE-2006-2453 Dia format string issues Solution : Get the newest Fedora Updates Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2007 Tenable Network Security |
||
|
Cables, Connectors |

Lot Of Two Vintage Apple Macintosh Computers Models 128k M0001 For Parts
$250.00
Macintosh Platinum Mouse - Apple 128K 512K 512Ke Mac Plus Lisa IIe M0100 - NEW
$44.99
1984 Apple Macintosh 128K Mac 512K RFI Foil Motherboard Shield 805-0577 REV. D
$24.99
Apple Macintosh 128k 512k Plus Analog Board Capacitor Re-Cap Kit - US Shipping
$23.95
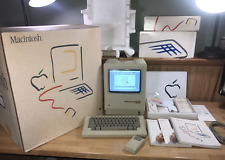
1984 APPLE MACINTOSH 128K 40th Anniversary MATCHING # BOX Set 1st Mac M0001 NICE
$7999.99
1984 Apple Macintosh 128K Mac 512K RFI Foil Motherboard Shield 805-0577 REV. D
$24.99
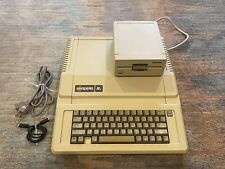
Vintage Apple lle 128k Enhanced Computer A2S2064 Rebuilt W/ Disk Drive & more
$359.99
Apple Macintosh M0001 128K computer & M0110 keyboard/mouse, for parts/repair
$300.00
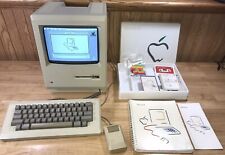
1984 APPLE MACINTOSH Model M0001 1st MAC 128K 40th Anniversary PICASSO KIT NICE
$4999.99
Apple Macintosh 128K M0001 Computer with Mouse, no keyboard. Case included. 1984
$512.13
|
||
|
No Discussions have been posted on this vulnerability. |