|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Fedora Local Security Checks >> Fedora Core 4 2005-894: xorg-x11 Vulnerability Assessment Details
|
Fedora Core 4 2005-894: xorg-x11 |
||
|
Check for the version of the xorg-x11 package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory FEDORA-2005-894 (xorg-x11). X.org X11 is an open source implementation of the X Window System. It provides the basic low level functionality which full fledged graphical user interfaces (GUIs) such as GNOME and KDE are designed upon. Update Information: Updated xorg-x11 packages that fix several integer overflows, various bugs, are now available for Fedora Core 4. X.Org X11 is an implementation of the X Window System, which provides the core functionality for the Linux graphical desktop. Several integer overflow bugs were found in the way X.Org X11 code parses pixmap images. It is possible for a user to gain elevated rights by loading a specially crafted pixmap image. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2005-2495 to this issue. Additionally, this update contains: - Support for some newer models of Intel i945 video chipsets. - A fix for a regression caused in the last Xorg update for Fedora Core 4, which resulted in some Matrox hardware to fail to initialize properly, which was introduced in the PCI config space access bugfix from the previous xorg-x11 update. The PCI config code has been updated now to handle BIOS related quirks of this nature, so this fix may also benefit users of some other brands of video hardware as well. - A fix for a memory leak in the X server's shadow framebuffer code. Solution : Get the newest Fedora Updates Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

Samsung Galaxy Tab A8 10.5" SM-X200 128GB Wifi Only Tablet Open Box
$149.99
Samsung Galaxy Tab A 8.0" 2019 SM-T290 32GB WiFi Tablet Open Box
$94.99
SAMSUNG M393A2G40DB0-CPB 16GB PC4-17000P DDR4-2133 2RX4 ECC
$14.95
Samsung - S Pen Creator Edition - White
$40.00
Genuine Samsung Book Cover Keyboard for 14.6" Galaxy Tab S8 Ultra | S8 Ultra 5G
$89.99
Samsung Galaxy Tab A9 (X110) 64GB 4GB RAM International Version (New)
$129.99
Samsung Galaxy Chromebook Go, 14-inch, 32GB, Unlocked All Carriers - Silver
$99.95
Samsung 16GB 2Rx4 PC3-12800R M393B2G70BH0-CK0 DDR3 RDIMM - SERVER RAM
$8.90
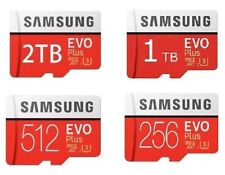
512GB SAMSUNG EVO Plus Micro SD MicroSDXC Flash Memory Card w/ SD Adapter
$21.99
Samsung Book Cover Keyboard Slim for Samsung Galaxy Tab S9+/S9 FE+ (5G) - Black
$65.99
|
||
|
No Discussions have been posted on this vulnerability. |