|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Fedora Local Security Checks >> Fedora Core 4 2005-768: epiphany Vulnerability Assessment Details
|
Fedora Core 4 2005-768: epiphany |
||
|
Check for the version of the epiphany package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory FEDORA-2005-768 (epiphany). epiphany is a simple GNOME web browser based on the Mozilla rendering engine * Wed Aug 17 2005 Marco Pesenti Gritti - Update to 1.6.5 - Remove patch integrated upstream Solution : http://fedoranews.org//mediawiki/index.php/Fedora_Core_4_Update:_epiphany-1.6.5-1 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

MOS 6502 CPU for Commodore VIC 20 Computer & 1541 & 1571 Tested US SELLER
$12.99
$200.00
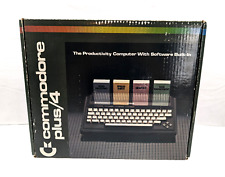
Commodore Plus 4 Computer Complete In Box (Tested Works)
$180.00
commodore 128, 128D, 128DCR A/V Breakout
$19.99
Commodore SX-64 W/Rare 1541 Flash Installed READ DESCRIPTION SX64 C-64
$459.00
$240.00
Commodore VIC 20 power cord (NEW REPLACEMENT POWER CORD AND CONNECTORS)
$14.99
Commodore 128 Slim 64k Video Ram Upgrade 41464-10 18Pin w/Sockets and TESTED
$9.95
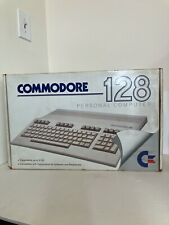
Vintage Commodore 128 Personal Computer w/Box 1987 Untested As Is Rare
$249.99
TeensyROM Cartridge for Commodore 64/128: MIDI, Fastload, Emulation, and Network
$65.00
|
||
|
No Discussions have been posted on this vulnerability. |