|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Fedora Local Security Checks >> Fedora Core 3 2005-1045: libungif Vulnerability Assessment Details
|
Fedora Core 3 2005-1045: libungif |
||
|
Check for the version of the libungif package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory FEDORA-2005-1045 (libungif). The libungif package contains a shared library of functions for loading and saving GIF format image files. The libungif library can load any GIF file, but it will save GIFs only in uncompressed format (i.e., it won't use the patented LZW compression used to save 'normal' compressed GIF files). Install the libungif package if you need to manipulate GIF files. You should also install the libungif-progs package. Update Information: The libungif package contains a shared library of functions for loading and saving GIF format image files. The libungif library can load any GIF file, but it will save GIFs only in uncompressed format it will not use the patented LZW compression used to save 'normal' compressed GIF files. A bug was found in the way libungif handles colormaps. An attacker could create a GIF file in such a way that could cause out-of-bounds writes and register corruptions. The Common Vulnerabilities and Exposures project assigned the name CAN-2005-2974 to this issue. All users of libungif should upgrade to the updated packages, which contain a backported patch to resolve this issue. Solution : Get the newest Fedora Updates Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
Asus TUF B365M-PLUS GAMING Motherboard LGA 1151 Intel B365 DDR4 M.2 Micro ATX
$65.00
MSI B450M-A PRO MAX II AM4 AMD B450 SATA 6Gb/s Micro ATX Motherboard
$68.99
GIGABYTE B560M DS3H AC LGA1200 Intel B560 SATA 6Gb/s Micro ATX Intel Motherboard
$64.99
Gigabyte AMD B550 UD AC Gaming Motherboard - AMD B550 Chipset - AM4 Socket - AMD
$89.99
Gigabyte GA-B85M-D3V Intel LGA1150 ATX DDR3 PCIe Desktop Motherboard w IO Shield
$29.99
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
Gigabyte Ultra Durable B550 GAMING X V2 Desktop Motherboard
$94.99
GIGABYTE MB10-Datto Motherboard Xeon D-1521- SR2DF 2.40 GHz- Open Box
$112.00
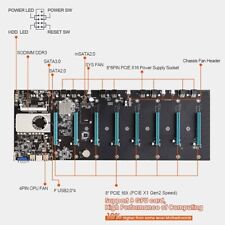
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
|
||
|
No Discussions have been posted on this vulnerability. |