|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Fedora Local Security Checks >> Fedora Core 2 2005-026: kernel Vulnerability Assessment Details
|
Fedora Core 2 2005-026: kernel |
||
|
Check for the version of the kernel package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory FEDORA-2005-026 (kernel). The kernel package contains the Linux kernel (vmlinuz), the core of any Linux operating system. The kernel handles the basic functions of the operating system: memory allocation, process allocation, device input and output, etc. CVE-2005-0001 Paul Starzetz from isec.pl found an exploitable hole in the x86 SMP page fault handler which could lead to privilege escalation. http://www.isec.pl/vulnerabilities/isec-0022-pagefault.txt This update additionally fixes a random memory corruption issue present in the previous update, and in addition updates to the latest -ac collection of patches. A full changelog of the update vs the previous -ac8 based release is available at http://lkml.org/lkml/2005/1/13/219 * Thu Jan 13 2005 Dave Jones - Update to 2.6.10-ac9 - Fix slab corruption in ACPI video code. * Mon Jan 10 2005 Dave Jones - Add another Lexar card reader to the whitelist. (#143600) - Package asm-m68k for asm-ppc includes. (don't ask). (#144604) Solution : http://www.fedoranews.org/blog/index.php?p=277 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

OEM Apple MacBook Pro 13 A1706 A1708 2017 LCD Screen Display Assembly Silver
$113.99
OEM Genuine Apple Macbook Pro 15" A1707 2016 2017 LCD Display Assembly Silver
$232.74
OEM Genuine Apple MacBook Pro A1990 2018 2019 15" LCD Screen Display Assembly
$218.49
NEW OEM A1494 Battery For Apple MacBook Pro 15" Retina A1398 Late 2014 2013
$54.99
Genuine Apple A1882 30W USB-C Power Adapter Apple OEM CHARGER
$18.99
Genuine Apple A1718 61W USB-C Power Adapter Apple OEM CHARGER
$24.99
Apple OEM Original (A1374) 45W MagSafe Power Adapter with Fold Plug Only - White
$10.95
OEM 61W USB C Type C Adapter Charger for Apple MacBook PRO 13" A1718 + Cable NEW
$23.00
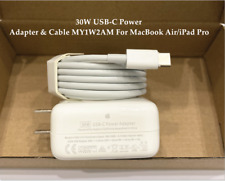
OEM 30W USB-C Power Adapter Charger for apple MacBook Air iPhone 11 12 Pro +Cord
$22.89
Genuine OEM Apple MagSafe 1 & 2 MacBook Pro/ MacBook Air Charger 85W| 60W |45W
$24.99
|
||
|
No Discussions have been posted on this vulnerability. |