|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Fedora Local Security Checks >> Fedora Core 2 2004-471: squirrelmail Vulnerability Assessment Details
|
Fedora Core 2 2004-471: squirrelmail |
||
|
Check for the version of the squirrelmail package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory FEDORA-2004-471 (squirrelmail). SquirrelMail is a standards-based webmail package written in PHP4. It includes built-in pure PHP support for the IMAP and SMTP protocols, and all pages render in pure HTML 4.0 (with no Javascript) for maximum compatibility across browsers. It has very few requirements and is very easy to configure and install. SquirrelMail has all the functionality you would want from an email client, including strong MIME support, address books, and folder manipulation. * Fri Nov 19 2004 Warren Togami 1.4.3a-6.FC2 - FC2 * Fri Nov 19 2004 Warren Togami 1.4.3a-7 - CVE-2004-1036 Cross Site Scripting in encoded text - #112769 updated splash screens * Thu Oct 14 2004 Warren Togami 1.4.3a-5 - default_folder_prefix dovecot compatible by default /etc/squirrelmail/config_local.php if you must change it * Wed Oct 13 2004 Warren Togami 1.4.3a-4 - HIGASHIYAMA Masato's patch to improve Japanese support (coordinated by Scott A. Hughes). - real 1.4.3a tarball * Tue Aug 31 2004 Warren Togami 1.4.3-2 - #125638 config_local.php and default_pref in /etc/squirrelmail/ to match upstream RPM. This should permit smoother drop-in replacements and upgrades. - other spec cleanup. Solution : http://www.fedoranews.org/blog/index.php?p=111 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

🍎🖥️ Vintage Apple III Computer - Works Great Monitor, Hard Drive, Software 🍎
$2000.00
MacEffects Gray ALPS Mechanical Keyboard for Vintage Apple IIe Computers
$195.00
Apple Macintosh M3501 M0312 AEKII Vintage Alps Keyboard (EARLY MODEL)
$79.99
Vintage Apple Certifited Apple Technical Coordinator T Shirt
$35.00
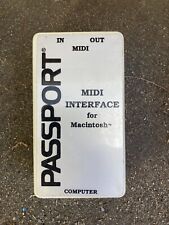
Vintage Passport MIDI Interface For Macintosh Mac Apple
$20.00
VINTAGE APPLE MACINTOSH POWERBOOK G3 UNTESTED NO POWER CORD
$60.00
Apple Macintosh ASK M0116 Vintage Keyboard Alps Keycaps (INCOMPLETE)
$14.99
Vintage Macintosh Classic Case Apple asset tag
$50.00
VINTAGE Apple Macintosh LC (FOR PARTS - DOES NOT BOOT) NO HDD #27
$49.99
Vintage Apple Newton MessagePad 2000 With Original Box and Some Accessories
$199.99
|
||
|
No Discussions have been posted on this vulnerability. |