|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> General >> Enhydra Multiserver Default Password Vulnerability Assessment Details
|
Enhydra Multiserver Default Password |
||
|
Enhydra Multiserver Default Admin Password Detailed Explanation for this Vulnerability Assessment This system appears to be running the Enhydra application server configured with the default administrator password of 'enhydra'. A potential intruder could reconfigure this service and use it to obtain full access to the system. Solution: Please set a strong password of the 'admin' account. Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2003 Digital Defense Inc. |
||
|
Cables, Connectors |

Atari 1050 5.25" Floppy Disk Drive Tested (w/Power cables)
$99.99
Vintage Family owned Atari 1200xl computer sold as is tested turns on with cable
$299.99
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
Vintage Atari 800XL ~ Home Computer in Original Box ~ Tested and Working
$149.90
Atari 800XL Computer with Chroma Added - Original Box - Tested and Working 100%
$225.00
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
Atari 600xl excellent condition - Video and RAM upgrades. 800XL compatible
$255.00
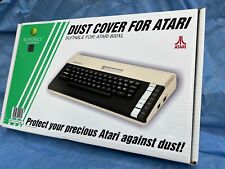
Atari 800XL - Transparent High Quality Dust Cover
$38.99
Atari ST Diagnostic Cartridge 520 1040 STF STFM Mega Computer cart test Diags
$28.75
Vintage Atari SH204 External 30MB Hard Drive Powers On UNTESTED Serial# 1005729
$99.99
|
||
|
No Discussions have been posted on this vulnerability. |