|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Drupal Comment Preview Code Execution Vulnerability (2) Vulnerability Assessment Details
|
Drupal Comment Preview Code Execution Vulnerability (2) |
||
|
Tries to execute a command via Drupal Detailed Explanation for this Vulnerability Assessment Summary : The remote web server contains a PHP application that permits execution of arbitrary code. Description : The version of Drupal installed on the remote host fails to properly validate previews on comments and permits access to more than one input filter, which is not true by default. A possible hacker can leverage this issue while previewing a comment to have it interpreted as PHP code, which will result in it being executed on the affected host with the rights of the web server user id. See also : http://drupal.org/node/113935 Solution : Upgrade to Drupal version 4.7.6 / 5.1 or later. Network Security Threat Level: Medium / CVSS Base Score : 6 (AV:R/AC:H/Au:NR/C:P/A:P/I:P/B:N) Networks Security ID: 22306 Vulnerability Assessment Copyright: This script is Copyright (C) 2007 Tenable Network Security |
||
|
Cables, Connectors |

ACASIS 2.5/3.5 inch 2 Bay SATA USB 3.0 Hard Drive Disk HDD SSD Enclosure 4 RAID
$58.99
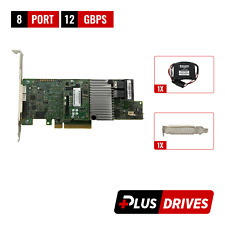
Intel PCIe SSD AIC RAID Controller Card G97168-252
$44.55
Cisco UCS LSI MegaRAID 9271CV-8I SAS2308 PCIe SAS Internal RAID Controller
$28.00
Oracle 7085209 LSI MegaRAID SAS 9361-8i 1GB Cache 12Gbps SAS/SATA PCIe RAID Card
$28.20
Inspur LSI 9300-8i Raid Card 12Gbps HBA HDD Controller High Profile IT MODE
$15.98
LSI MegaRAID 9361-8i 12Gb PCIe 8-Port SAS/SATA RAID 1Gb w/BBU/CacheVault/License
$39.95
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$82.49
Apple Xserve 14-Bay RAID Network Storage Array Enclosure NO HDD A1009 #2
$335.00
4 Bay RAID External Hard Drive Enclosure for 2.5/3.5" SATA HDD/SSD
$79.99
|
||
|
No Discussions have been posted on this vulnerability. |