|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> DokuWiki dwpage.php Accessibility Vulnerability Vulnerability Assessment Details
|
DokuWiki dwpage.php Accessibility Vulnerability |
||
|
Checks whether DocuWiki dwpage.php is accessible via http Detailed Explanation for this Vulnerability Assessment Summary : The remote web server contains a PHP script that should be removed or protected. Description : The remote host is running DokuWiki, an open-source wiki application written in PHP. The installed version of DokuWiki includes a script, 'bin/dwpage.php', that is intended as a commandline tool for modifying pages. By accessing it through the web, an unauthenticated remote attacker can abuse it to view local files and even execute arbitrary code, both subject to the rights of the web server user id. See also : http://retrogod.altervista.org/dokuwiki_2006-03-09b_cmd.html http://milw0rm.com/exploits/2322 http://www.freelists.org/archives/dokuwiki/09-2006/msg00064.html Solution : Limit access to DokuWiki's 'bin' directory using, say, a .htaccess file or remove the affected script. Network Security Threat Level: High / CVSS Base Score : 7 (AV:R/AC:L/Au:NR/C:P/A:P/I:P/B:N) Networks Security ID: 19911 Vulnerability Assessment Copyright: This script is Copyright (C) 2006-2007 Tenable Network Security |
||
|
Cables, Connectors |

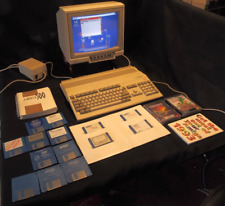
Mini External OLED AMIGA Gotek Floppy Drive Emulator For Amiga 500/500+/600/1200
$37.24
Amiga 500 Gotek Custom Mount USB Floppy Emulator - Complete Kit with Gotek
$65.00
Amiga MiniMig 2.0 - FPGA Amiga 500 with real 68000CPU
$179.99
Commodore Amiga CD32 Power Supply 100v-240v NEW
$38.00
Commodore Amiga 500 with Original Box. Power Supply Games and More 1 MEG No.2
$463.19
AT&T Card w/ Motorola 060 XC68060RC50A 68060 & Seagate ST51080N SCSI2 Hard Drive
$324.95
$299.95
Apollo Vampire 600v2 / 600 V2 FPGA Accelerator Card for Commodore Amiga 600
$350.00
AMIGA 500 COMPUTER COMMODORE Complete in Box Powers/untested Good Condition
$370.00
Amiga 5.25 External DUAL SLIM Floppy Disk Drive VERY RARE
$199.00
|
||
|
No Discussions have been posted on this vulnerability. |