|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SNMP >> Default community names of the SNMP Agent Vulnerability Assessment Details
|
Default community names of the SNMP Agent |
||
|
Default community names of the SNMP Agent Detailed Explanation for this Vulnerability Assessment Summary : The community name of the remote SNMP server can be guessed. Description : It is possible to obtain the default community names of the remote SNMP server. A possible hacker may use this information to gain more knowledge about the remote host, or to change the configuration of the remote system (if the default community permit such modifications). Solution : Disable the SNMP service on the remote host if you do not use it, filter incoming UDP packets going to this port, or change the default community string. Network Security Threat Level: High Networks Security ID: 11237, 10576, 177, 2112, 6825, 7081, 7212, 7317, 9681, 986 Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

Vintage Dream Writer NTS 325 Computer Basic Language Notebook “Untested “
$30.00
Vintage Sun SunBlade 100 Workstation UltraSPARC IIe 1.6GB 20GB HD 380-0467-01
$150.00
Vintage Compaq 141649-004 2 Button PS/2 Gray Mouse M-S34 - FAST SHIPPING - NEW
$8.99
Datacomp DCK 84 BRAND NEW Vintage Keyboard
$39.00
Vintage Apple LisaDraw Brochure, very nice condition
$40.00
Vintage Classic Apple Macintosh System Boot Install Disk Floppy/CD *Pick Version
$10.39
Apple II GS A2S6000 Vintage Computer Powers On
$125.00
Vintage PC USA & PC Globe 3.0 5.25” Floppy Disk Demos 1990 PC Globe Inc.
$15.00
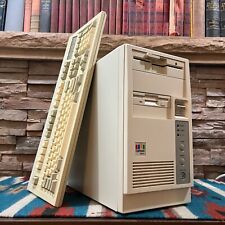
Vintage Retro AT PC Tower - Intel 486 4MB 3.5" 5.25" OPL Sound Keyboard POSTS
$199.00
$150.00
|
||
|
No Discussions have been posted on this vulnerability. |