|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA956] DSA-956-1 lsh-server Vulnerability Assessment Details
|
[DSA956] DSA-956-1 lsh-server |
||
|
DSA-956-1 lsh-server Detailed Explanation for this Vulnerability Assessment Stefan Pfetzing discovered that lshd, a Secure Shell v2 (SSH2) protocol server, leaks a couple of file descriptors, related to the randomness generator, to user shells which are started by lshd. A local attacker can truncate the server's seed file, which may prevent the server from starting, and with some more effort, maybe also crack session keys. After applying this update, you should remove the server's seed file (/var/spool/lsh/yarrow-seed-file) and then regenerate it with "lsh-make-seed --server" as root. For security reasons, lsh-make-seed really needs to be run from the console of the system you are running it on. If you run lsh-make-seed using a remote shell, the timing information lsh-make-seed uses for its random seed creation is likely to be screwed. If need be, you can generate the random seed on a different system than that which it will eventually be on, by installing the lsh-utils package and running "lsh-make-seed -o my-other-server-seed-file". You may then transfer the seed to the destination system as using a secure connection. The old stable distribution (woody) may not be affected by this problem. For the stable distribution (sarge) this problem has been fixed in version 2.0.1-3sarge1. For the unstable distribution (sid) this problem has been fixed in version 2.0.1cdbs-4. We recommend that you upgrade your lsh-server package. Solution : http://www.debian.org/security/2006/dsa-956 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is (C) 2007 Michel Arboi |
||
|
Cables, Connectors |

Samsung Galaxy Tab A8 10.5" SM-X200 128GB Wifi Only Tablet Open Box
$149.99
Samsung Galaxy Tab E 8" 16GB Black SM-T377V (Verizon) Android Tablet IG1000
$31.95
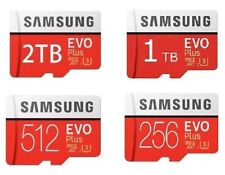
2TB SAMSUNG EVO Plus Micro SD MicroSDXC Flash Memory Card w/ SD Adapter
$9.99
Genuine Samsung Book Cover Keyboard for 14.6" Galaxy Tab S8 Ultra | S8 Ultra 5G
$89.99
Samsung USB 3.1 Flash Drive Bar Plus 256gb TITAN Gray
$24.10
Samsung Galaxy Tab A9 (X110) 64GB 4GB RAM International Version (New)
$129.99
Samsung PM983a M.2 22110 SSD NVMe PCIe 3.0x4 1.88TB
$88.50
Samsung - S Pen Creator Edition - White
$40.00
512GB SAMSUNG EVO Plus Micro SD MicroSDXC Flash Memory Card w/ SD Adapter
$21.99
SAMSUNG 24" Monitor Full HD LED/LCD - GRADE A CONDITION - S24E650PL
$69.95
|
||
|
No Discussions have been posted on this vulnerability. |