|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA928] DSA-928-1 dhis-tools-dns Vulnerability Assessment Details
|
[DSA928] DSA-928-1 dhis-tools-dns |
||
|
DSA-928-1 dhis-tools-dns Detailed Explanation for this Vulnerability Assessment Javier Fernández-Sanguino Peña from the Debian Security Audit project discovered that two scripts in the dhis-tools-dns package, DNS configuration utilities for a dynamic host information System, which are usually executed by root, create temporary files in an insecure fashion. The old stable distribution (woody) does not contain a dhis-tools-dns package. For the stable distribution (sarge) these problems have been fixed in version 5.0-3sarge1. For the unstable distribution (sid) these problems have been fixed in version 5.0-5. We recommend that you upgrade your dhis-tools-dns package. Solution : http://www.debian.org/security/2005/dsa-928 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is (C) 2007 Michel Arboi |
||
|
Cables, Connectors |

VINTAGE APPLE MACINTOSH POWERBOOK 180 ( M4440) Powers On
$100.00
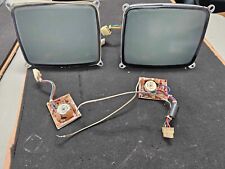
2x Lot Vintage Retro Apple Macintosh Classic II SE SE/30 Screen Replacement Good
$89.98
Vintage Mac Apple Computer 25 Disc Lot OS Install Adobe Mini Iwork
$30.00
2x Vintage Apple Mac Sony MP-F75W 2MB & MP-F51W 3.5" Floppy Disk w/ Caddy & Sled
$99.98
Vintage Apple Power Macintosh G4 Empty Tower Case Graphite
$29.95
VTG Apple Macintosh Plus 1Mb - UNTESTED
$70.00
Vintage Data Desk Turbo 101 keyboard 60420-6 mac PC
$75.00
Vintage Apple iMac G3 M5521 Mac OS 9.0.4 256MB Blue Please Read
$150.00
VINTAGE APPLE Macintosh Performa 6400/180 Desktop Computer (M3548) - CHIMES
$79.99
Vintage Apple IIc Mac Macintosh Computer Modem A9M0300 w/ RARE Power Supply
$39.99
|
||
|
No Discussions have been posted on this vulnerability. |