|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA921] DSA-921-1 kernel-source-2.4.27 Vulnerability Assessment Details
|
[DSA921] DSA-921-1 kernel-source-2.4.27 |
||
|
DSA-921-1 kernel-source-2.4.27 Detailed Explanation for this Vulnerability Assessment Several local and remote vulnerabilities have been discovered in the Linux kernel that may lead to a denial of service or the execution of arbitrary code. The Common Vulnerabilities and Exposures project identifies the following problems: Alexander Nyberg discovered that the ptrace() system call does not properly verify addresses on the amd64 architecture which can be exploited by a local attacker to crash the kernel. A problem in the offset handling in the xattr file system code for ext3 has been discovered that may permit users on 64-bit systems that have access to an ext3 filesystem with extended attributes to cause the kernel to crash. A vulnerability has been discovered in the ptrace() system call on the amd64 architecture that permits a local attacker to cause the kernel to crash. A vulnerability has been discovered in the stack segment fault handler that could permit a local attacker to cause a stack exception that will lead the kernel to crash under certain circumstances. Ilja van Sprundel discovered a race condition in the IA32 (x86) compatibility execve() systemcall for amd64 and IA64 that permits local attackers to cause the kernel to panic and possibly execute arbitrary code. Balazs Scheidler discovered that a local attacker could call setsockopt() with an invalid xfrm_user policy message which would cause the kernel to write beyond the boundaries of an array and crash. Vladimir Volovich discovered a bug in the zlib routines which are also present in the Linux kernel and permits remote attackers to crash the kernel. Another vulnerability has been discovered in the zlib routines which are also present in the Linux kernel and permits remote attackers to crash the kernel. A null pointer dereference in ptrace when tracing a 64-bit executable can cause the kernel to crash. Andreas Gruenbacher discovered a bug in the ext2 and ext3 file systems. When data areas are to be shared among two inodes not all information were compared for equality, which could expose wrong ACLs for files. Chad Walstrom discovered that the ipt_recent kernel module to stop SSH bruteforce attacks could cause the kernel to crash on 64-bit architectures. An error in the NAT code permits remote attackers to cause a denial of service (memory corruption) by causing two packets for the same protocol to be NATed at the same time, which leads to memory corruption. The following matrix explains which kernel version for which architecture fix the problems mentioned above: We recommend that you upgrade your kernel package immediately and reboot the machine. Solution : http://www.debian.org/security/2005/dsa-921 Network Security Threat Level: High Networks Security ID: 14477 Vulnerability Assessment Copyright: This script is (C) 2006 Michel Arboi |
||
|
Cables, Connectors |

Extron RGB-160XI Analog Computer Video 60-378-01
$187.06
Vintage 1960s Donner Model 3000 Analog Computer ~ MUSEUM PIECE Extremely Rare
$4000.00
NEW Aquarius+ Computer Signature Edition - 8Bit Retro System
$239.00
Apple Macintosh SE/30 M5119 Computer 8MB RAM Recapped Working *See Description*
$450.00
IBM Modem Saver Phone Line Tester
$7.99
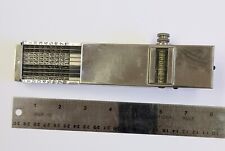
Landen Computer. Circa 1898. the Rapid Computer Company. With Original Case.
$425.00
Burr Brown Analog Computer parts Circuit boards w Helipot Potentiometers 1631a
$85.00
Apple IIc Analog Board NOS - 661-0265
$74.00
Sony Trinitron CPD-1304 9 PIN Analog Vintage CRT Monitor - Great for Retro PC
$475.30
Macintosh Classic/Classic II Analog Board Computer 630-0395 New
$276.00
|
||
|
No Discussions have been posted on this vulnerability. |