|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA900] DSA-900-3 fetchmail Vulnerability Assessment Details
|
[DSA900] DSA-900-3 fetchmail |
||
|
DSA-900-3 fetchmail Detailed Explanation for this Vulnerability Assessment Due to restrictive dependency definition for fetchmail-ssl the updated fetchmailconf package couldn't be installed on the old stable distribution (woody) together with fetchmail-ssl. Hence, this update loosens it, so that the update can be pulled in. For completeness we're including the original advisory text: Thomas Wolff discovered that the fetchmailconf program which is provided as part of fetchmail, an SSL enabled POP3, APOP, IMAP mail gatherer/forwarder, creates the new configuration in an insecure fashion that can lead to leaking passwords for mail accounts to local users. This update also fixes a regression in the package for stable caused by the last security update. For the old stable distribution (woody) this problem has been fixed in version 5.9.11-6.4 of fetchmail and in version 5.9.11-6.3 of fetchmail-ssl. For the stable distribution (sarge) this problem has been fixed in version 6.2.5-12sarge3. For the unstable distribution (sid) this problem has been fixed in version 6.2.5.4-1. We recommend that you upgrade your fetchmail package. Solution : http://www.debian.org/security/2005/dsa-900 Network Security Threat Level: High Networks Security ID: 15179 Vulnerability Assessment Copyright: This script is (C) 2007 Michel Arboi |
||
|
Cables, Connectors |

Vintage DEC/The Redac mini cabinet front panel Digital Equipment Corp. 19"
$269.99
VINTAGE DEC DIGITAL DISK FOR RK 05 HARD DRIVE / DECPACK 2200 BPI-16
$95.00
DEC VINTAGE DIGITAL EQUIPMENT CORPORATION VT100 TERMINAL & KEYBOARD AS-IS
$198.99
DEC PDP 8/M PDP 8M / 4 avail / Vintage Digital Equipment Corp /Also DEC PDP 12
$5775.00
DEC DIGITAL Equipment Corp VT220-D2 Vintage CRT Terminal
$215.00
Vintage DEC Digital RX 180 AB Dual 5.25" Disk Drive
$149.00
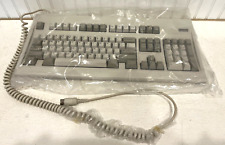
Digital Equipment Corporation DEC-2000 Vintage Keyboard - NOS NEW in Plastic
$119.95
VINTAGE DEC DIGITAL M7940 DLV11 QBUS SERIAL LINE UNIT BOARD PDP11/03 PDP11/23
$99.00
VINTAGE DEC Digital RK11-D DISK CONTROL M7255 PDP 11 (B1)
$129.99
VINTAGE DEC Digital DN11-AA Backplane 70-08513
$139.99
|
||
|
No Discussions have been posted on this vulnerability. |