|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA755] DSA-755-1 tiff Vulnerability Assessment Details
|
[DSA755] DSA-755-1 tiff |
||
|
DSA-755-1 tiff Detailed Explanation for this Vulnerability Assessment Frank Warmerdam discovered a stack-based buffer overflow in libtiff, the Tag Image File Format library for processing TIFF graphics files that can lead to the execution of arbitrary code via malformed TIFF files. For the old stable distribution (woody) this problem has been fixed in version 3.5.5-7. For the stable distribution (sarge) this problem has been fixed in version 3.7.2-3. For the unstable distribution (sid) this problem has been fixed in version 3.7.2-3. We recommend that you upgrade your libtiff packages. Solution : http://www.debian.org/security/2005/dsa-755 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Toshiba 512GB SSD Solid State Drive 2.5" SATA THNSNC512GBSJ Sun Oracle 7010845
$53.99
P13695-B21 HPE 2TB NVMe x4 RI SCN 2.5'' DS SSD P45631-001 P10591-002 **Retail**
$399.00
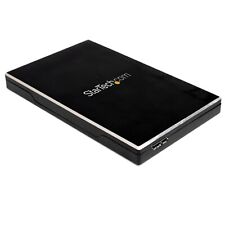
StarTech SAT2510BU32 2.5" SuperSpeed USB 3.0 SSD SATA Hard Drive Enclosure
$24.99
SanDisk 2TB Ultra 3D NAND SSD, Internal Solid State Drive - SDSSDH3-2T00-G26
$149.99
Patriot P210 128GB 256GB 512GB 1TB 2TB 2.5" SATA 3 6GB/s Internal SSD PC/MAC Lot
$14.99
Intel DC S3510 Series 120GB SSD 2.5" 6Gb/s SATA Solid State Drive SSDSC2BB120G6K
$9.99
Netac 1TB 2TB 512GB Internal SSD 2.5'' SATA III 6Gb/s Solid State Drive lot
$13.99
Fanxiang SSD 512GB 1TB 2TB 4TB 2.5'' SSD SATA III Internal Solid State Drive lot
$13.99
Fanxiang 256GB 512GB 1TB 2TB 4TB Internal SSD 2.5" SATA III 6GB/s for PC/MAC Lot
$188.09
Fanxiang 4TB 2TB 1TB SSD 550MB/s 2.5'' SATA III Internal Solid State Drive lot
$209.99
|
||
|
No Discussions have been posted on this vulnerability. |