|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA422] DSA-422-1 cvs Vulnerability Assessment Details
|
[DSA422] DSA-422-1 cvs |
||
|
DSA-422-1 cvs Detailed Explanation for this Vulnerability Assessment The account management of the CVS pserver (which is used to give remote access to CVS repositories) uses a CVSROOT/passwd file in each repository which contains the accounts and their authentication information as well as the name of the local unix account to use when a pserver account is used. Since CVS performed no checking on what unix account was specified anyone who could modify the CVSROOT/passwd could gain access to all local users on the CVS server, including root. This has been fixed in upstream version 1.11.11 by preventing pserver from running as root. For Debian this problem is solved in version 1.11.1p1debian-9 in two different ways: Additionally, CVS pserver had a bug in parsing module requests which could be used to create files and directories outside a repository. This has been fixed upstream in version 1.11.11 and Debian version 1.11.1p1debian-9. Finally, the umask used for &ldquo cvs init&rdquo and &ldquo cvs-makerepos&rdquo has been changed to prevent repositories from being created with group write permissions. Solution : http://www.debian.org/security/2004/dsa-422 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Vintage AST Ascentia 900N 4/50 CS10 Notebook UNTESTED no cables
$29.99
Intel Celeron 300 333 MHz SL2YP SL2X8 SL2WN SL2WN SL2Y2 vintage CPU GOLD
$10.95
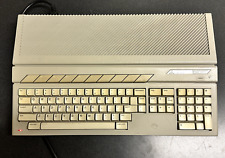
Vintage Atari 1040STf COMPUTER POWERS ON
$94.99
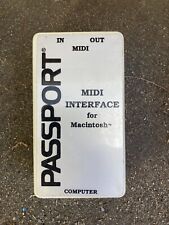
Vintage Passport MIDI Interface For Macintosh Mac Apple
$20.00
Vintage Gateway Solo2150 Laptop - Windows 98 Era
$40.00
AT Tower Computer Case, MEV 120 HX, CLEANED Vintage For 386/486/Pentium, READ
$99.99
Apple Macintosh ASK M0116 Vintage Keyboard Alps Keycaps (INCOMPLETE)
$14.99
Apple Macintosh AEKII M3501 Vintage Keyboard Alps Keycaps (INCOMPLETE)
$14.99
Vintage Comfort Keyboard Systems Ergomagic Mechanical AT/PS2 Keyboard
$149.99
IBM PCjr 4860 JR Vintage PC Desktop Computer W/ Power Cord & Keyboard, *READ
$154.99
|
||
|
No Discussions have been posted on this vulnerability. |